The flaw affected 30 access point models and four firewall series, allowing hackers to block and take control of devices.
Zyxel, a network device manufacturer, thanked Nikita Abramov, a Positive Technologies security researcher, for discovering six hardware vulnerabilities, five of which have a high severity level. The vendor was notified of the threat as part of the responsible disclosure policy and released patches to fix the issues.
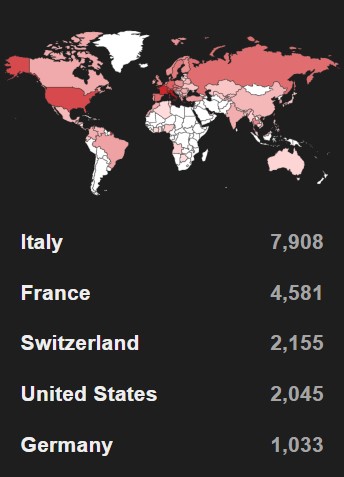
According to Positive Technologies, 23,000 devices might have been affected.1 Almost 8,000 such systems were found in Italy, another 4,500 in France, and over 2,000 in the Czech Republic and the United States.
"CVE-2023-22913 and CVE-2023-22916 present the highest threat, with a CVSS v3.1 score of 8.1," explained Nikita Abramov, Application Analysis Expert at Positive Technologies. "These two bugs allowed an attacker to remotely inject arbitrary system commands into the application code and execute them on the firewall. As a result, the intruder could cause a device failure by triggering a denial-of-service state, disable some security features, or change configuration data. Any of these events pose a serious threat to the normal operation of the firewall. Another way of exploiting unprotected devices is botnet deployment. Such botnets are widely used by hackers."
The next two vulnerabilities, CVE-2023-22915 and CVE-2023-22917, scored 7.5 out of 10. If exploited, the former could lead to a denial-of-service state of the firewall, while the latter allowed a malicious file to be uploaded, granting hackers control over the device. CVE-2023-22914 was assigned a slightly lower severity score (7.2). Through this vulnerability, an authenticated attacker with administrator privileges could execute unauthorized operating system commands in one of the folders used for storing temporary firewall files.
Yet another vulnerability—CVE-2023-22918—got a score of 6.5 and proved dangerous for Zyxel firewalls and access points alike. It could allow an authenticated attacker to obtain encrypted administrator information from the device. Using this information together with publicly available scripts, intruders can decrypt data, including user passwords.
To fix the vulnerability, follow the vendor’s recommendations.
Earlier in 2023, Zyxel already eliminated four weaknesses found by Nikita Abramov in several series of Wi-Fi routers and other devices.
- The experts counted the number of devices with vulnerable firmware that are visible on the Internet, but some of their functions affected by the vulnerabilities might be disabled by default.
