Six days of more than 70 talks and roundtables brought over 20,000 visitors
By the end of the last day of the battle at The Standoff, attackers had successfully breached the perimeter of all six organizations and gained persistence on corporate networks. But they had a harder time with triggering business risks thanks to the work of experienced defender teams. Systems were taken offline at the airport, amusement park, gas distribution station, oil company, and power plant. The business center and bank were hit as well. While hackers were able to show materials of their choosing on billboards, the port and railroad remained intact.
Here we will give our round-up of all the action at The Standoff. Online talks included experts speaking on such topics as gaining physical access to a building, faking a voice in five seconds, recovering ransomed files, intercepting smartphone data on 5G, and much more.
Meanwhile, in the cyber-range competition, the winning attacker team was Codeby (27,123 points), followed by back2oaz (24,463 points) and DeteAct (18,508 points). Collectively, the attackers were able to trigger 47 percent of all the risks that had been designed. Of the 24 unique triggered cyber-risks, 2 were novel and unanticipated by the organizers. The jury accepted more than 50 task completion reports from attacker teams.
Defender teams were able to detect more than 200 security incidents on their respective infrastructures. Incident detections were highest for the teams IZ:SOC and CT&MM. The teams performed 21 investigations. The average investigation took 11 hours and 50 minutes from start to finish.
All of the mock city's companies had to grapple with the aftermath of cyberattacks. Here are some of the most serious cases:
- At the Nuft petrochemical plant, an accident led to toxic leakage. Attackers were able to gain access to the plant's controls and closed the refrigeration intake, which caused overheating and disrupted the chemical manufacturing process. Soon after, the attackers were able to halt the process entirely.
- A cyberattack disabled oil extraction equipment, causing production to stop. The attackers also accessed the oil storage controls and disrupted the process for transport of oil to storage tanks. They later were also able to disable the controller responsible for managing petrochemical transport.
- At the 25 Hours amusement park, the Ferris wheel fell over. A team gained access to the controls and increased the rotation speed to the highest value, causing the Ferris wheel to collapse. They finished by disabling the Ferris wheel's controller and turning off lighting to prevent visitors from leaving.
- Bank attacks enabled theft of funds from individuals' accounts, as well as theft of data regarding bank clients (name, account balance, card PAN, etc.).
- Valuable documents were stolen from two companies. Employee personal data was stolen from five companies.
- During the closing minutes of the competition, back2oaz accessed climate controls for the office buildings and could change the temperature settings.
- Some risks were made possible by poorly protected corporate websites. These include disruptions to the amusement park's online ticketing offices, as well as plane ticket sales and passenger check-in systems on the airport website.
- However, the majority of risks required first accessing the company's local network. Here, too, we see that attackers started by looking for vulnerabilities in web applications in order to breach infrastructure. Defender teams reported on successful attempts to exploit such vulnerabilities.
- The first vulnerability was found by n0x in a Nuft system just 19 minutes after the start of the competition. The jury received a total of 433 bug bounty reports. Almost half were SQL injection, while a quarter involved remote code execution. Two thirds of all vulnerabilities were found at the city's Nuft and Big Bro Group.
The largest number of risks (8) was triggered at 25 Hours, the mock company that owned the city's business center, HVAC system, traffic lights, and amusement park. The runner-up, with seven unique risks triggered, was oil company Nuft.
Only the railroad and port escaped unscathed.
Life and limb at risk in one third of cases
According to Maxim Filippov, Director for Russian Business Development at Positive Technologies, a third of the risks at the cyber-range could have caused some form of physical harm to people. At the Kommersant business session during The Standoff, he noted some of the novel aspects added to this year's competition.
Filippov said: "Every business modeled on the cyber-range has certain risks associated with it: disruption of operations, leak of personal data, loss of confidential documents, and so on. There are no ready-made attack vectors here. Instead, we create a space for red teams with freedom of action to hack and probe systems. We observe as they hack, analyze traffic, and build their attack chains. The result is valuable insight that then gets distilled into our products."
Dmitry Serebryannikov, Director of Security Analysis at Positive Technologies, added: " We did not expect half of the risks to be triggered. That's a lot, particularly given that we had little time. This year, the level of attackers has really increased."
Mikhail Pomzov, Director of Knowledge Base and Expertise at Positive Technologies, explained in more detail: "This year, the job of defenders was to prove their ability to monitor an incident at every stage. Their overarching aim was to keep an eye on the functioning of services and, as quickly as possible, fix any disruptions caused by the attackers' actions. The defenders were evaluated based on the number of attacks they detected, average incident investigation time, and infrastructure uptime—after all, the longer that services are down, the worse defenders are coping and the more damage is being done by attackers."
Hacking doors, banks, and 5G
Many hackers dream of gaining physical access to hardware or facilities. Robert Sell, President of Trace Labs, in his talk described the eight steps taken by attackers to obtain physical access to a facility of interest. He showed how criminals (or pentesters) scope out their target, along with the pretexts they have ready in case they are caught. He also talked about tools for breaking and entering, plus ways to cache them in the target building for later use.
Today's banks should be less worried about their vault doors and more about their information security. Timur Yunusov, Head of Research at Cyber R&D Lab, demonstrated how many banks are poorly protected against fraud, complete with real examples of attacks on European banks costing hundreds of thousands (or even millions) of euros. Timur analyzed the typical mistakes made by security and risk management teams in the financial sector, along with real-world advice on how to avoid issues. The latest and most complicated solutions—such as machine learning—are often unneeded when it comes to stopping many threats to banks. Instead, banks simply need to follow time-proven steps to address specific vulnerabilities and take a hard look at how much they lose from specific attacks in order to prioritize security efforts.
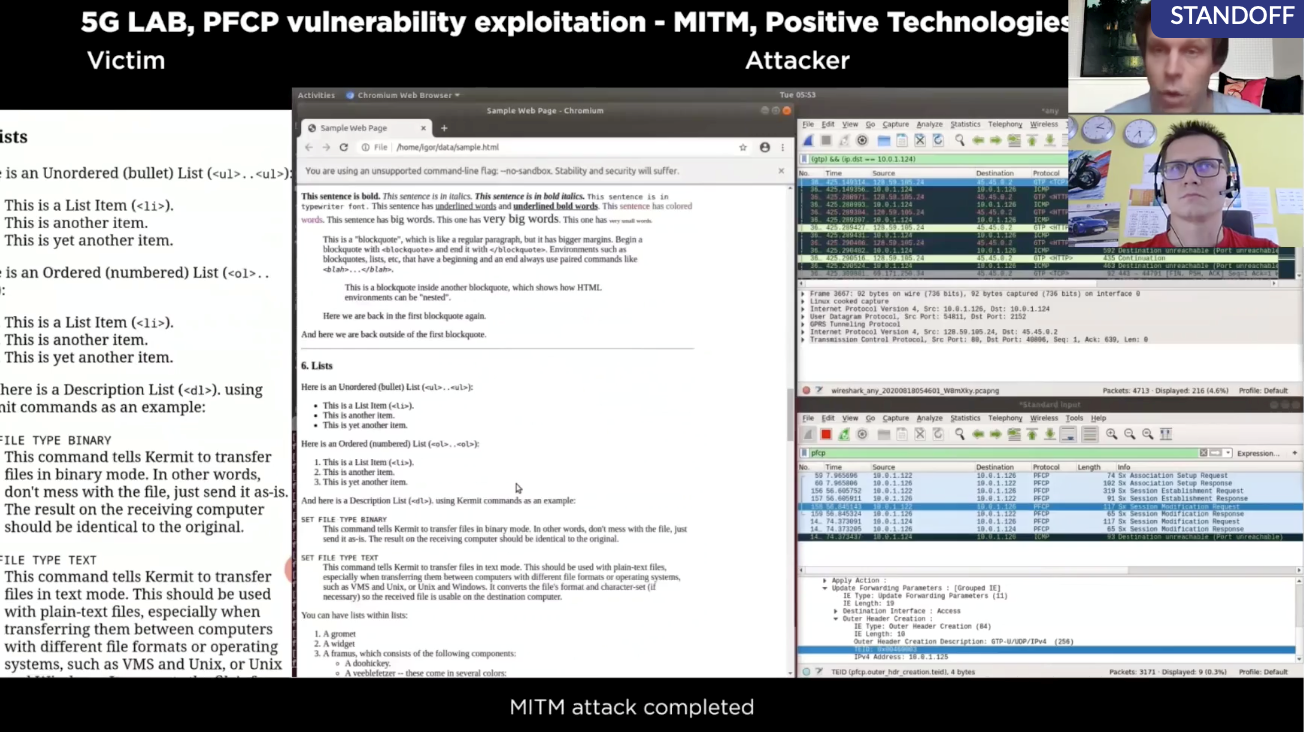
5G offers a long list of benefits, among them smart transportation, traffic management, and improved road safety. Telemedicine is another young field that promises to benefit from the new technology. But there's an utter lack of knowledge on the information security aspects of smart cars and e-surgery, as noted by CTO at Positive Technologies. As he said, "I would not want for my kids to be riding in a bus when its autopilot gets hacked." He pointed out that, since the 5G architecture is highly dependent on previous-generation networks, all of yesterday's vulnerabilities in those networks will remain dangerous tomorrow. During his talk, he showed how a man-in-the-middle (MITM) attack targeting vulnerabilities in the PFCP protocol can intercept data from a 5G-connected smartphone and announced new 5G security research due out by year's end.
Ransomware dilemmas
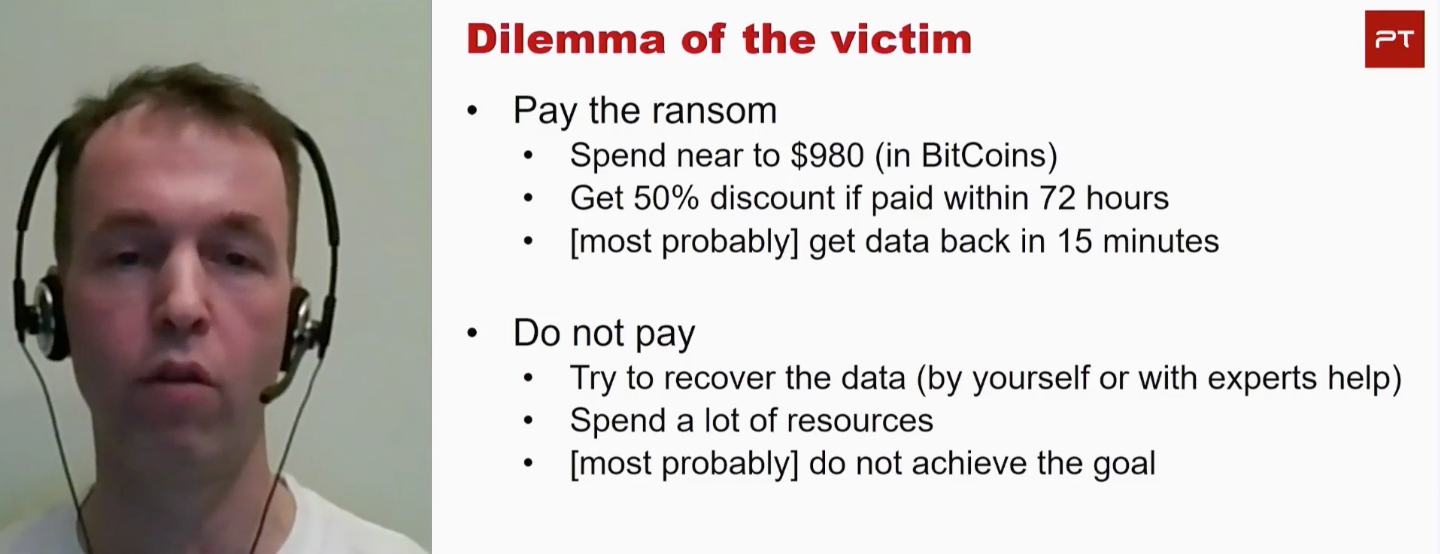
Unknown attackers used the STOP (Djvu) ransomware to encrypt files on a computer belonging to a friend of Dmitry Sklyarov, Head of Application Analysis at Positive Technologies. The attackers demanded a Bitcoin ransom equivalent to $980. His friend, after deciding that "there's no negotiating with terrorists," asked Dmitry for help. In his talk, Dmitry told how he was able to recover the data and find online keys for helping victims of STOP (Djvu) using different cryptographic methods.
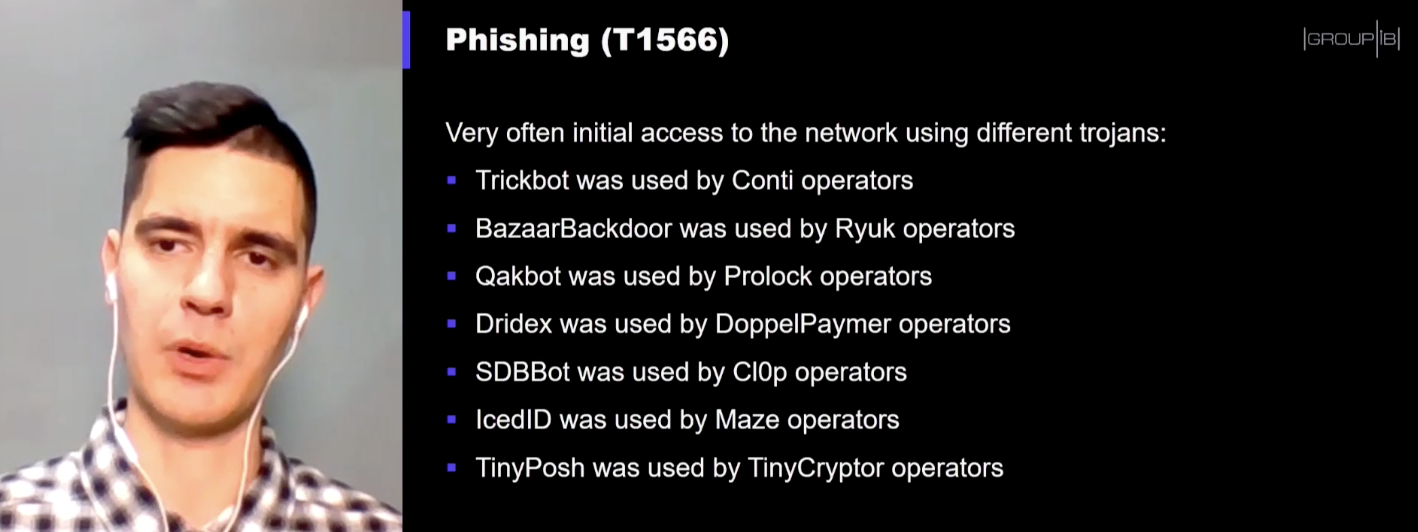
The topic of ransomware was continued by Oleg Skulkin, Senior Digital Forensic Analyst at Group-IB. His talk covered the tactics, techniques, and procedures used by various ransomware operators in 2020 such as Conti, Ryuk, Prolock, DoppelPaymer, CI0p, Maze, and TinyCryptor. He noted the growing prominence of ransomware in the past year. An enormous amount of new ransomware has been released and targets include such major companies as Canon and Garmin. As a result, ransoms are reaching unheard-of levels. Garmin, for instance, had to pay out $10 million.
This point of view was echoed by Costin Raiu, Director of the Global Research and Analysis Team (GReAT) at Kaspersky. "Ransomware in 2017 did not ask for large amounts (only $100 to $300) and the targets were individuals and their personal computers. But since late 2017, this trend has changed and attacks have become more sophisticated." One trend he sees this year is publication by hackers of encrypted data in an effort to blackmail victims: "This is why companies are driven to pay millions of dollars in order to avoid reputational risks."
Costin also called upon ransomware victims to refrain from negotiating with attackers or paying ransom. There are no guarantees that data will be decrypted even if the victim does pay up. Instead, he encourages reaching out to nomoreransom.org, which is a global project for researchers to decrypt encrypted data free of charge with any tools that are available.
"Even if there are no tools now, they may appear later. And of course, don't forget to archive your data and keep it on inaccessible offline storage," he advised.
Sergey Golovanov, Principal Security Researcher at Kaspersky, commented: "In 2020, when criminals breach computers for financial gain, they aren't trying to suck the money out themselves, as was the case in years past. Now they are encrypting the data and demanding that the victim pay bitcoins." Besides ransomware, another trend he highlighted was exploitation of vulnerabilities in remote access software. Attackers this year have also started to hone in on home computers as a way to access corporate infrastructure.
Fake voices, fake faces
Machine learning is being wielded by both attackers and defenders in the digital realm. Vyacheslav Gordeev, Systems Engineer at Fortinet, reviewed technologies including machine learning, neural nets, and deep learning. These are used for filtering spam, passively analyzing traffic, searching for malware, or defending web applications. Attackers are also taking advantage of these technologies to forge biometric data (voices and faces), bruteforce passwords, and search for vulnerabilities.
Fake biometrics were at the center of the talk by BBVA Next Technologies security researchers Miguel Hernández Boza and José Ignacio Escribano Pablos. They demonstrated techniques, algorithms, and tools (most of them open-source) to generate and detect fake data including audio, text, images, and video.
Already, there are publicly available tools for cloning a voice based on just five seconds of audio, inserting faces into a video, or creating unique avatars. All this can be weaponized against individuals and organizations. Creating fake identities is getting easier and combatting them is becoming harder. The two researchers showed the limitations of different tools and techniques for creating synthetic data, which may be of use to security professionals trying to perform detection.
Threats related to dynamic rendering were the topic of Vasily Ermilov, security researcher at American startup r2c. Dynamic rendering is generally used to provide crawlers (such as a Google, Slack, or Twitter bot) with pre-processed site pages to improve search engine rankings. But incorrectly configured dynamic rendering opens the door to server-side request forgery (SSRF) attacks. Little effort from attackers is required and, even worse, dynamic rendering is always used for the most important and popular site pages. Vasily described his experience looking for vulnerabilities in Rendertron, which resulted in him gaining control of a live production application. He also talked about how to use open-source tools to speed up the hunt for bugs.
New security approaches from Microsoft
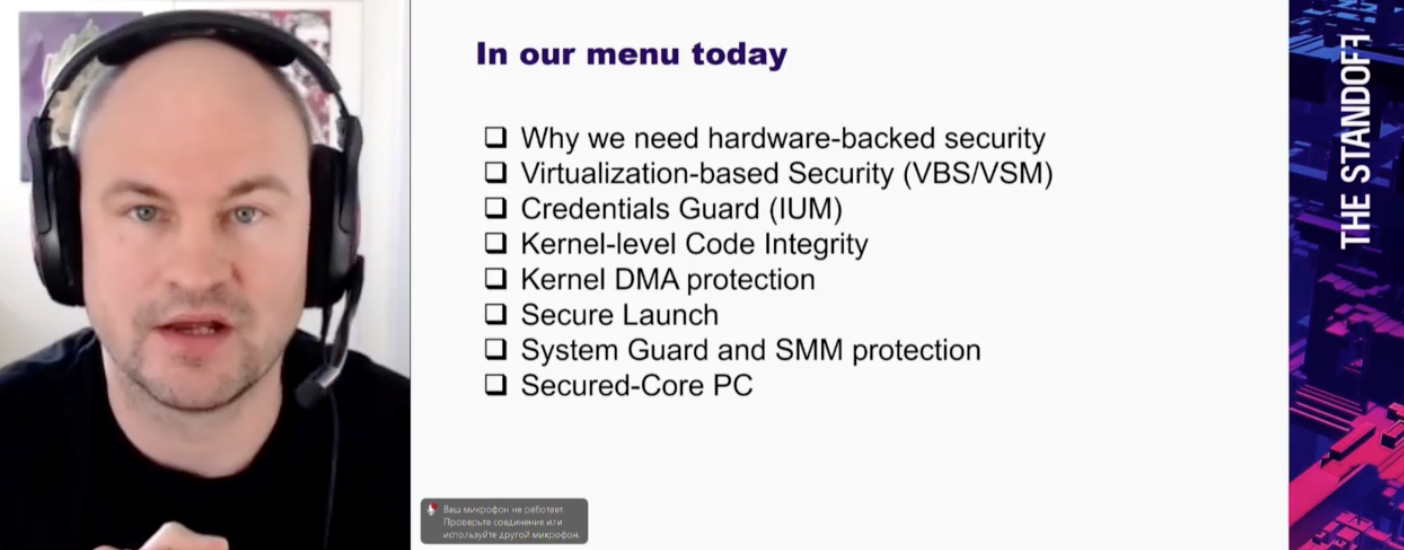
Attackers are burrowing down to the firmware level and trying to compromise the system startup process. One example is the BootHole vulnerability. In 2018, the Strontium group exploited firmware vulnerabilities. Hardware security in Windows 10 was the subject of a talk from Artem Sinitsyn, Microsoft Head of Information Security Programs in Central and Eastern Europe. The Secured-core PC (SecOps) initiative supports creation of Windows 10 computers that are defended from firmware-level attacks. These systems should be able to perform biometric identification to prevent data loss, safely store critical information including credit card data, defend against bootkits, and more. Besides the Microsoft Surface, Secured-core PCs currently on the market include models from Dell, Dynabook, HP, Lenovo, and Panasonic.
Artem also described the large number of Microsoft bug bounty programs for boosting security across its Identity, Windows, Xbox, Azure, Dynamics, and Microsoft Edge businesses. He went into the details of guidelines for identifying and publishing potential vulnerabilities, plus what researchers should know before making Coordinated Vulnerability Disclosure (CVD) submissions.
Threats to developers
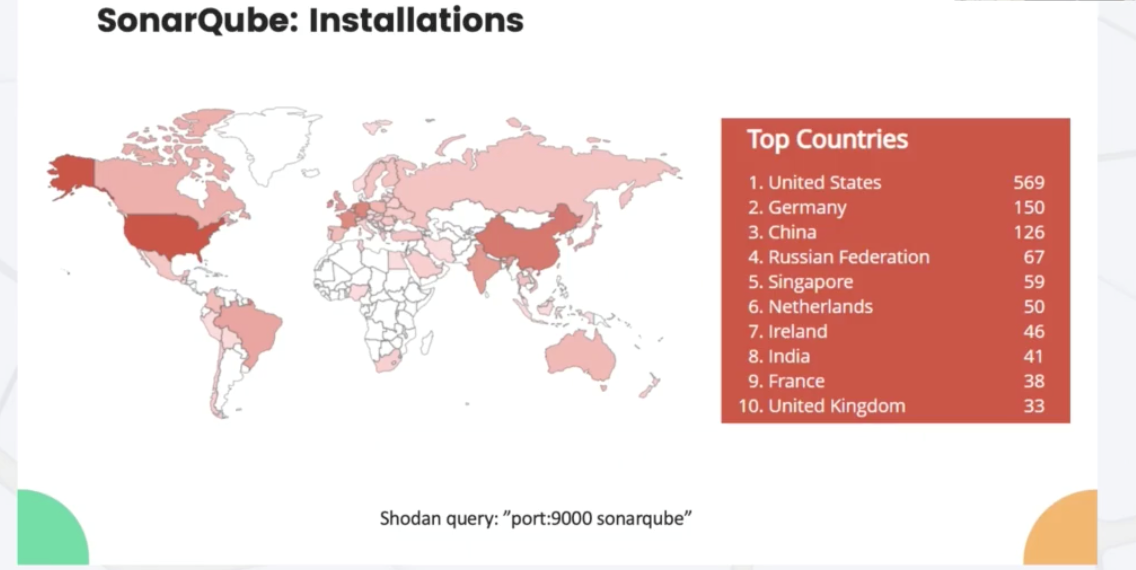
Popular code inspection and security scanner products can actually offer a point of entry to APT groups. Denis Makrushin, Head of Advanced Security Research at Huawei, singled out SonarQube, an open-source platform for analyzing the quality and security of software code. A simple "port:9000 sonarqube" query on Shodan turns up hundreds of Internet-accessible installations, some of which do not require any authentication at all. This gives attackers wide-open access to any code being developed or audited. In some cases, using Shodan is not necessary at all.
Developers and QA engineers upload many scripts with sensitive information to public repositories. These scripts, with a bit of GitHub scraping (such as a query resembling "product_name+pass"), can yield credentials, private keys, or certificates ("domain_name+private"). One example is a commercial Gartner quadrant solution, Checkmarx, for which installations can be detected with a "CxWebclient" query. All too often, these installations are open to all comers. Monitoring and remediation of such leaks can be the job of a dedicated secret management solution such as Hashicorp Vault.
QA engineers were also mentioned in the talk by Serguei Gorokhov, Security Architect at EPAM. He emphasized the importance of secure development processes, which depend on excellent communication between AppSec and Security Testing teams: "When assessing risks, drafting requirements, modeling threats, or designing the architecture, testers should be sitting at the same table as developers and providing them with assistance."
Malware researcher Stanislav Rakovsky addressed an issue impacting software developers. Attackers can modify PyInstaller files and insert a payload. PyInstaller files are used when a developer wants to distribute Python files in a way independent of user environment and interpreter. Stanislav noted that besides the payload, the embedded interpreter can be modified to include anti-debugging tools and to check for antivirus products so that malware can lie low in hostile environments. Discovering such changes in an interpreter would be extremely difficult.
Needle in a haystack
What does data enrichment do for security incidents? It helps to set priorities, direct alerts appropriately, and respond smartly to security events. But enrichment is a very real case of "garbage in, garbage out." Aleksandr Kuznetsov, Key Project Manager at Rostelecom-Solar, pointed out that when security operations center (SOC) operators receive incorrect or incomplete data, this data ends up in the incident file and slows down investigation. According to Aleksandr, the best data sources include Kaspersky Security Center and IPAM, AD DS, TIP, and EDR solutions. In his view, CMDB solutions are not yet up to the task. Working from home is complicating enrichment efforts, since employees are frequently changing locations, equipment, and dynamic IP addresses. This has caused major changes in enrichment priorities. If there is nothing in place for incident enrichment currently, companies can start with a simple Excel spreadsheet, but mature infrastructures would be better served by IRP or SOAR systems.
Alexey Novikov, Director of the PT Expert Security Center, during the roundtable on SOCs, noted: "A good SOC is doing its job when its employees see how they might get attacked and know which tactics and techniques are currently being used by hackers. You have to constantly be educating yourself, studying new material, and thinking about how to thwart attackers. This is constant mental exercise combined with the drive to be the best at monitoring and incident investigation."
In his talk, malware researcher Raman Ladutska spoke about how his team has analyzed the activity of Dridex, one of the largest botnets today. Determining the botnet's next victim takes analyzing malicious documents, looking for command and control (C2) servers and domains, monitoring their relationships with other botnets, and spotting activity peaks. Raman gave numbers confirming the benefits of this approach and explained how security specialists can apply it in their own work.
Yury Maksimov, Positive Technologies CEO, summed up: "The Standoff has come into its own as a cyber-range where dozens of offensive and defensive teams are revved up and saying that yes, this is the real thing! This cyberbattle proved to be an incredibly realistic model of real life. Whole new opportunities are opening up. Our products for detecting threats, blocking attacks, and investigating incidents were exposed for the first time to this incredibly challenging environment. We all walked away with one-of-a-kind experience that will help to make security products smarter. And smarter products will give people back time to create."
This iteration of The Standoff is all over, but a detailed write-up of the competition is forthcoming. So keep up with us on standoff365.com as well as Twitter, LinkedIn, Facebook, and YouTube. Daily summaries from the event are available at the Standoff website (first two days, second two days).
At The Standoff, top-tier offensive and defensive security specialists battle each other in a mock digital city. The cyber-range contains full-fidelity replicas of the production chains, business scenarios, and technology landscape typical of different industries. A wide range of real businesses will be recreated at The Standoff 2020, including logistics, transportation (cargo and passenger), energy extraction and distribution, smart city systems, finance, telecom, and more. Companies and security professionals alike benefit from participating in The Standoff by empirically testing the feasibility of cyberattacks in a safe environment, gaining knowledge and hands-on skills to detect and counter threats, gaming out response scenarios, and seeing first-hand the close relationship between cybersecurity and business.
Learn more at standoff365.com.
