Contents
What is the Standoff 365 Bug Bounty platform?
Standoff 365 Bug Bounty is a platform where researchers find and report security vulnerabilities for a reward, giving you an effective way to make sure your IT infrastructure is safe. Standoff 365 Bug Bounty is also a place where researchers interact with each other. Positive Technologies takes care of all the technicalities, such as facilitating money transfers to winners on behalf of companies.
Standoff 365 Bug Bounty was first launched at Positive Hack Days on May 18, 2022. Since then, 7,537 researchers have registered on the platform.
Programs
As of November 12, 2023, Standoff 365 Bug Bounty features 53 programs (four of which are already archived) of organizations operating in various industries: IT, commerce, finance, and government agencies. Most of these programs, however, cover the IT industry, government sector, and education platforms.
A major Russian grocery chain named Azbuka Vkusa and Positive Technologies were the first companies to put their programs on the platform in May 2022. The number of programs has grown significantly over time, reaching 17 in Q3 2022 and 40 by the end of that year, and continues to grow today.
The conditions and requirements for each program are determined by the Standoff 365 Bug Bounty team and a representative of the company in question. They include the amount of the reward, the list of non-tolerable events, program scope, bug hunter requirements, and more. This way, the platform takes care of most of the routine needs, creating a comfortable environment for each organization.
Reward statistics
For bug hunters, the most important aspects of the program are total payout and the highest possible reward (for the most severe vulnerability).
The maximum payout can vary hugely from program to program: one company may pay $100 for a critical vulnerability, while another may pay tens of thousands of US dollars. The size of the reward depends on the company's revenues, size, and the information it handles. So far, IT companies and financial organizations have paid out more to hackers than companies in other industries. Collectively, they account for 81% of rewards, despite being represented in only 44% of programs.
*Positive dream hunting is a program by Positive Technologies in which participants are asked to steal money from the company's accounts, which represents a non-tolerable event for the company. Positive Technologies offers 30 million rubles for triggering this non-tolerable event. Although not included in the chart, this unusual program offers the highest reward of all.
The Standoff 365 Bug Bounty rewards are comparable to those paid out on global platforms. Below is an example of rewards offered on the HackerOne platform.
Vulnerabilities found
One of the key indicators that the platform is performing well is the number of valid reports on the found vulnerabilities. Valid reports are reports verified by the platform and a program representative. Since the platform's launch, bug hunters have submitted 1,479 reports that have been accepted by program representatives, 10% (152) of which contained critical vulnerabilities and 19% (287)—high-severity vulnerabilities.
* N/A is related to reports that mention vulnerabilities that do not have a significant negative impact on the company's infrastructure. There is usually no reward for such reports.
In the year and a half that Standoff 365 Bug Bounty has been running, hackers have found 71 Common Weakness Enumeration (CWE) vulnerabilities in web applications. In the table below, CWE vulnerabilities are ranked by the percentage of reports out of the total number of reports submitted. This is an important indicator due to the fact that attackers use various tactics and methods, meaning the more various flaws are identified, the more secure the infrastructure is.
CWE-79, Improper neutralization of input during web page generation (Cross-site scripting), ranked first as it was mentioned in 22% of reports.
| Rank | CWE-ID | Name | Description | Negative consequences: |
|---|---|---|---|---|
| 1 | CWE-79 | Improper neutralization of input during web page generation (Cross-site scripting) | The application does not neutralize or incorrectly neutralizes user (attacker) input before it is placed in output. This output can be represented as a web page that is seen by other users (victims). | Instead of data, attackers often send malicious code that can be executed in other users' browsers, which allows attackers to steal data, including information about victim sessions |
| 2 | CWE-284 | Improper access control | The application does not restrict or incorrectly restricts access to a resource from an unauthorized actor (attacker). | Access control involves the use of:
|
| 3 | CWE-200 | Exposure of sensitive information to an unauthorized actor | The application exposes sensitive information to an actor (attacker) who is not authorized to access that information. | Configuration Information Disclosure |
| 4 | CWE-918 | Server-side request forgery (SSRF) | The web server receives a URL or similar address from an attacker and sends a request to this address. However, the web server does not check whether the request is being sent to the secure destination. | Attackers can make it seem that the requests are sent from the web server. The server can be used to conduct port scanning of hosts in the internal network, access files in the system, or collect information about the infrastructure. |
| 5 | CWE-287 | Improper authentication | The application fails to check or incorrectly checks that the user is who they claim to be. The attacker bypasses verification by faking cookies and tokens used as credentials. | The attacker gains access to the application functionality that is normally controlled by the user the hacker is impersonating. |
HackerOne keeps its own CWE statistics. The company ranks vulnerabilities by the number of reports that mention these flaws. The data from the two platforms is similar. Therefore, Standoff 365 Bug Bounty supports global trends even in statistics about vulnerabilities in companies' infrastructures.
Standoff Hacks
The most important thing about a bug bounty program is the community of hackers and their level of professionalism. For the most qualified researchers, Standoff holds private Standoff Hacks events, offering bug bounty programs with brand-new applications and higher rewards.
The last such event was held in Sochi. In two weeks, 30 researchers earned over $125,000, with the most prolific researcher gaining $34,000.
Next year, three Standoff Hacks are planned, and a special preliminary round will be laid out for potential participants. White hackers will be very welcome!
Standoff 365 Bug Bounty is the largest bug bounty platform in Russia
The infographic below covers some characteristics of the main bug bounty platforms in Russia.
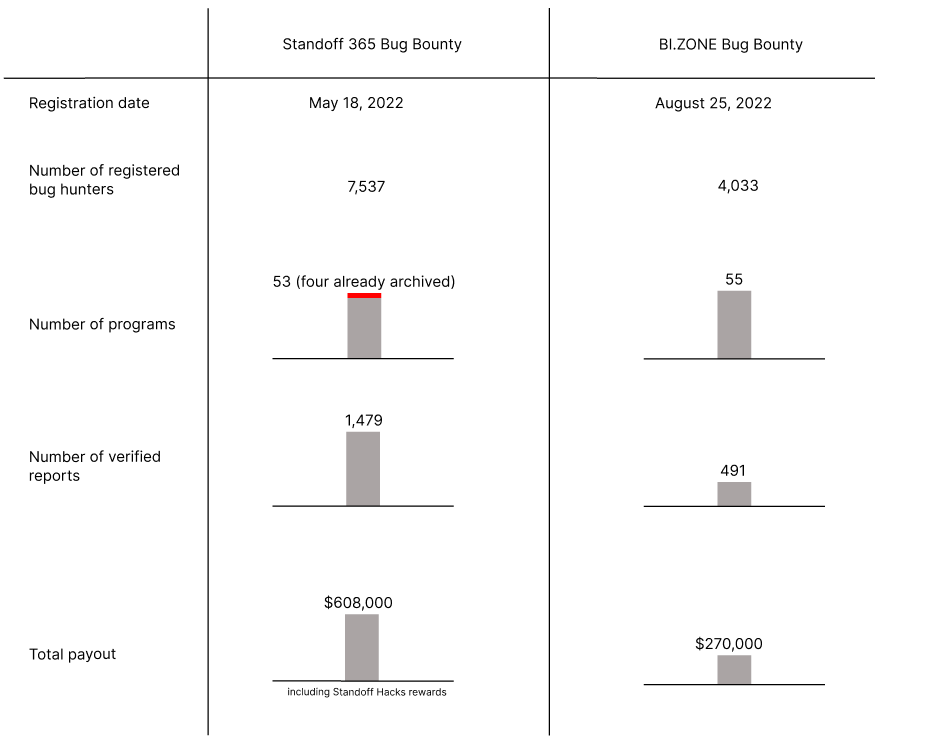
It is also possible to determine the top five most successful (in terms of reward gained) bug hunters on each platform.
Conclusion
Even the smallest companies need cybersecurity, as business processes may suffer from non-tolerable events that can potentially be triggered by attackers.
Ethical hackers from around the world are ready to help organizations find vulnerabilities in their systems and infrastructures and prevent non-tolerable events being triggered in real attacks. That's why businesses are opening their own bug bounty programs. These programs can be hosted on a special platform or launched by the companies on their own. The second approach requires a lot of effort, so more often than not, businesses choose the first option.
This is where Standoff 365 Bug Bounty, a fast-growing platform by Russia's leading cybersecurity company Positive Technologies, comes in. The growing platform is a one-stop shop for businesses who want to put their programs to the test, and simplifies operational overhead by taking charge of all the organizational tasks including setting up the program's terms and conditions and handling many of the legal issues.
