Contents
Africa is a region experiencing rapid economic development. Over the past twenty years, the combined GDP of the region has increased more than fivefold, from USD 695.88 billion in 2002 to USD 2.98 trillion in 2022. GDP growth for 2023 is estimated at 3–4% and is projected to exceed USD 4 trillion by 2027. The cumulative growth of African economies reflects the region's huge potential and is contributing to an increase in demand for Internet and digital services.
At the same time, the development of the digital sphere in the region has outpaced the development of laws and regulations regarding cybersecurity. The increasing frequency and complexity of cyberattacks in the African region threatens the security of critical information infrastructure and demands urgent action to strengthen protection measures. Failure to counter cyberthreats can have serious consequences for individuals, businesses and the socio-economic development of the continent. In this report, we will look at the main cybersecurity challenges in the African region and explore possible ways to build a resilient and secure digital environment.
Summary
- The digital environment in the African region is rapidly evolving, but the lack of proper measures for ensuring cybersecurity, an insufficient legislative framework in the field of information security, and a low level of awareness about cybersecurity issues among the general population are leading to an increase in the number of cyberthreats.
- Africa's low level of preparedness to counter cyberthreats costs the concerned countries on average 10% of their GDP.
- Financial organizations are the primary target of cybercriminals, with almost one in five (18%) successful attacks on organizations directed at this sector. As a rule, the attackers are pursuing financial gain. Telecommunication companies are also facing a considerable number of attacks (13%) due to their growing customer base, which makes them attractive targets for data theft and extortion.
- The use of ransomware remains one of the most serious threats in the region. One of the main vectors of delivery is the compromise of computers, servers, and network equipment (74%). This indicates the low security of companies, namely vulnerabilities in the network perimeter and сonfiguration flaws in externally available services.
- Attacks using social engineering, including Business Email Compromise (BEC) pose the primary cyberthreat to organizations and individuals. More than half of the groups conducting BEC attacks operate in Africa and are familiar with the region's characteristics.
- On underground forums, cybercriminals actively buy and sell access to the networks of major African organizations, such as government and financial institutions, trade enterprises, and IT companies. The average cost of access with domain administrator privileges is around USD 300, while access with local administrator privileges goes for around USD 170. Also on these cybercriminal markets, attackers share and offer to sell databases containing information about employees and customers of various companies.
- African organizations regularly face DDoS attacks, with government and financial institutions being particularly affected. These attacks are typically carried out by hacktivists.
- Both hacktivists and organized criminal groups operate in the region, pursuing financial motives or engaging in cyberespionage. Financial difficulties are pushing the younger generation to look for ways to earn money quickly; the increasingly low entry threshold for engaging in cybercrime thus makes this a tempting prospect.
- The lack of effective international cooperation and information exchange between African countries is hindering the fight against cybercrime.
- Recommendations for governments to strengthen their cybersecurity include developing national-level policies and strategies in the field of information security, forming legislative regulation for personal data protection, protecting critical information infrastructure, and establishing national cyberincident response teams. In addition, strengthening international collaboration to ensure cybersecurity is essential.
- Recommendations for organizations to enhance their cyberresilience include identifying non-tolerable events and protecting critical assets, monitoring and responding to cyberthreats with modern security tools, and evaluating the effectiveness of implemented measures, and training employees. Investing in the development of cyberspecialists and participating in cyberexercises will also play a crucial role in improving the cybersecurity of African organizations.
Digital transformation and cybersecurity challenges in the region
In recent years, Africa has seen a rapid proliferation of digital technologies, especially in the areas of financial technology and e-commerce. The COVID-19 pandemic also played a role in this, creating the need to provide the possibility of remote working for many employees. In 2021, 43% of Africa's population (612 million people) had Internet access.
What's more, there is huge potential in the African continent regarding technology, especially due to its young population: about 60% of Africa's population in 2020 was under 25 years old. This factor encourages the use of new technologies. According to the 2021 study by the GSMA, the number of unique mobile subscribers in sub-Saharan Africa will reach 615 million by 2025. Furthermore, estimates for the entire region indicate that the number of Internet users will exceed 1 billion people by 2023. The Digital Transformation Strategy for Africa aims to ensure that by 2030 every inhabitant of the region will have stable access to the Internet.
Key sectors of the economy, including finance, education, agriculture, government, security, and manufacturing, are actively adopting digital technologies and transitioning their operations to online platforms. In accordance with the Digital Transformation Strategy for Africa, cybersecurity and personal data protection are fundamental principles in the implementation of the digital transformation project. However, the widespread use of technology, combined with insufficient cybersecurity measures, inadequate legislation in the field of information security, and a low level of public awareness concerning information security, creates favorable conditions for cybercriminals. Moreover, many African countries are facing economic constraints, making it difficult to allocate sufficient funds for cybersecurity.
In recent years, there has been a significant increase in cybercrime worldwide: according to our data, the total number of successful cyberattacks has more than doubled over the past five years. This rise in cyberincidents is also evident among African countries. In the second quarter of 2023, Africa experienced the highest average number of cyberattacks per week per organization, with a 23% increase compared to the same period in 2022. Cyberattacks can lead to events that are intolerable for businesses and governments, such as halting of business operations, large-scale theft of funds, and leaks of confidential data. The financial losses from cyberattacks are substantial, and according to ECA data, UNECA: United Nations Economic Commission for Africa in 2022 Africa's low level of preparedness for cyberthreats cost countries an average of 10% of their GDP.
One of the most serious problems facing Africa is the lack of information security infrastructure. About 90% of African businesses operate without cybersecurity protocols, making them vulnerable to cyberthreats. Experts recognize the need to change the approach to cybersecurity in Africa as it undergoes digital transformation.
Many African countries have not yet developed legislation covering all aspects of information security, making it difficult to effectively deal with cyberthreats and complicating the implementation and enforcement of cybersecurity measures. To date, only 39 out of 54 African countries have implemented cybersecurity legislation, and two countries are in the drafting stage of legislation. The adoption of cybersecurity policies and regulations across the entire continent is 72%, the lowest level in the world. Only 14 countries have ratified the African Union Convention on Cyber Security and Personal Data Protection.
According to a KPMG survey, approximately 75% of respondents from African organizations reported having cybersecurity strategies that were either updated regularly or developed according to the organization's threat profile with measurable KPIs. At the same time, 78% of IT department heads believe that their organization is not ready to fend off cyberattacks, despite increasing investments in security. Another problem is the acute shortage of cybersecurity specialists: as of 2020, there was an estimated shortage of at least 100,000 certified professionals.
With the increasing availability of the Internet in Africa, an increase in the activities of international organized cybercrime networks in the region is to be expected. Moreover, given the high unemployment rate, the young population may join already existing cybercriminal groups to make a quick buck. Lack of awareness about cybersecurity among the general population, inadequate measures to counter attacks in organizations, and poor cooperation between the law enforcement agencies of different countries make the continent's more digitally-developed countries an attractive target for attackers.
Victims and consequences of attacks
The main targets of attackers
In the period from the beginning of 2022 to the first half of 2023, among the various sectors of the economy, the most targeted organizations were those in the financial sector (18% of attacks on organizations), followed by telecommunications companies (13%), government agencies (12%), and organizations from the trade (12%) and industrial (10%) sectors.
15% of successful attacks targeted individuals
Cyberattacks The research covered only successful cyberattacks (incidents) with negative impact on a certain company or an individual targeted major companies such as Flutterwave, TransUnion, and the headquarters of Porsche in South Africa, as well as Eskom and the Electricity Company of Ghana (ECG). Cybercriminals also attacked important government structures: the Bank of Zambia, several ministries in Uganda, government institutions in Ethiopia and Senegal.
Targeted attacks accounted for 68% of successful cyberattacks. In these cases, the perpetrators were focused on a specific organization or industry.
The consequences of attacks affect entire regions
Most often, attacks were aimed at obtaining confidential information: 38% of companies experienced this. Criminal actions also frequently caused disruptions in organizational operations: for example, in every third successful attack, the main activities of companies were disrupted (35%). 7% of incidents resulted in direct financial losses.
The consequences of successful cyberattacks can vary significantly. Their impact can range from affecting a single individual to disrupting the functioning of entire industries or regions. The events that could have catastrophic effects for an organization differ case-by-case; for example, for banks, it could be large-scale theft or scams targeting users, while for industrial enterprises, it could be disruptions to technological processes with serious consequences for citizens.
A non-tolerable event is an event that occurs as a result of a cyberattack and prevents achieving the operational and strategic goals of the organization or leads to a prolonged disruption of its main activities.
Finance sector
The financial sector attracts the most criminals, with 18% of all attacks targeting organizations within it. This is firstly because criminals are primarily interested in financial gain, which, coupled with the relatively low level of security of these companies, makes them attractive targets. Moreover, financial organizations store large amounts of customer data, including payment information, allowing attackers to use stolen information for further attacks on users.
One of the major campaigns aimed at financial institutions was reported by experts in the fall of 2022. Between 2018 and 2022, the OPERA1ER group OPERA1ER (also known as DESKTOP-GROUP, Common Raven, NXSMS, or Bluebottle) is a French-speaking financially motivated group that has been operating since 2016. They primarily target payment gateways and the SWIFT international interbank system in their attacks. The group's victims include more than ten African countries, such as Ivory Coast, Nigeria, Senegal, and Uganda. The criminals use spear phishing and various types of malware (usually open-source) to carry out their attacks. carried out more than 35 successful attacks and stole at least USD 11 million from banks and telecom providers in several countries, with African banks being the most frequent victims. The total damage from the attacks is estimated at USD 30 million. Typically, the criminals aimed to compromise operator accounts with access to significant sums of money. The criminals then used the stolen credentials to transfer funds.
Another case came to light this summer: members of a fraudulent syndicate were apprehended after hacking more than a thousand bank accounts of customers in Nigeria. The suspects confessed to using specialized software to hack into customers' accounts and make discreet money transfers from any bank. This attack underscores how important it is for banks and other financial institutions to ensure the security of infrastructure and eliminate vulnerabilities in business processes and software used. This in order to protect both the organization itself and its customers.
Financial sector leaders acknowledge the seriousness of cyberthreats. According to 2023 Africa Financial Industry Barometer survey, cybersecurity ranks as the number one risk factor in the financial services sector for the second year in a row. About 97% of heads of large financial institutions in Africa consider cybercrime a significant threat along with macroeconomic conditions and political and social instability. The proliferation of cyberattacks and their increasing complexity are making cybersecurity a top priority for financial institutions. Financial institutions are the largest employers of cybersecurity professionals in the region, but only 24% of organizations believe they have sufficient resources to counter attacks.
Telecommunications
Telecommunications is the second most attractive industry for cybercriminals, and for good reason: the significant increase in customers of telecommunications companies across the continent allows attackers to have a serious impact on both individual companies and entire regions. This increase in customers also leads to the availability of more user information, including personal and payment data as well as data about connections. Criminals attack organizations to disrupt their operations and demand ransom for restoring systems, as well as to steal user data.
In February 2023, cybercriminals attacked the Internet service provider RSAWEB. The criminals encrypted the company's data and demanded a ransom to decrypt it. The attack caused a significant disruption to RSAWEB's services, leaving some customers unable to access the Internet for several days. Experts believe that the company was subjected to a large-scale attack on VMware ESXi software; cybersecurity agencies around the world had previously issued warnings that attackers were actively targeting VMware ESXi servers that had not yet installed security updates. Presumably, the attackers exploited the CVE-2021-21974 vulnerability in their attacks.
Companies must take measures to prevent the exploitation of vulnerabilities and the occurrence of non-tolerable events. To achieve this, we recommend paying attention to the vulnerability management process in the organization. This will help to promptly identify weaknesses in critical assets, as well as eliminate vulnerabilities that are popular among attackers—before they are exploited and cause serious consequences for the company.
Government institutions
Government agencies have traditionally been a favorite target for attackers: according to our data, this industry accounted for 17% of successful attacks on organizations worldwide in 2022. Government institutions are significant objects of urban infrastructure, which makes them a frequent target for hacktivists. Another important point is that government agencies store data about citizens.
In the spring, as a result of an attack by the BlackCat group The BlackCat group (also known as ALPHV) distributes a ransomware program of the same name, and also provides it under the "ransomware as a service" (RaaS) model. Victims around the globe include organizations in industry, trade, transport, insurance, service, telecoms, as well as government and medical institutions. the internal network of the African Union headquarters was paralyzed, and the attackers managed to spread malware to more than 200 computers. This incident occurred ten days after the closing of the annual summit of the organization, which brings together the heads of the continent's states. Had the attackers struck earlier, such an important event for the African Union could have been disrupted. Restoring the systems required the intervention of experts from Interpol, Afripol and the African Bank.
Retail
In attacks on organizations in the trade industry, the attackers are primarily focused on stealing customer data, particularly personal and payment information. In African regions, cybercriminals were able to steal confidential information in 86% of successful attacks against organizations in the trade sector.
In May of last year, cybercriminals managed to steal about 3.7 million customer records from a major pharmacy retailer, Dis-Chem Pharmacies. In this incident, attackers were able to gain access to the data by compromising a third-party service provider. While researching the world's current cyberthreats, we regularly come across news of successful attacks on organizations in which the attackers managed to compromise the supply chain or trusted communication channels. According to our data, in 2022 this method was used in 4% of successful attacks on organizations worldwide and was most popular in the trade industry, accounting for 8% of attacks on the sector. Two-thirds of successful attacks that started with compromising a trusted party resulted in leaks of confidential information, and 4 in every 10 cases led to disruptions to the organization's core activities.
When building protection against cyberattacks, it is important to take into account not only your own security, but also the security of partners, suppliers, and contractors. We recommend setting equal requirements for the information security of your counterparties as for your own infrastructure.
Manufacturing and industry
Cybercriminals target the industrial sector due to the importance of technological processes, as well as the scale of impact both on individual companies and on entire industries, regions and countries. Advanced technologies and the use of digital services and software increase the chances for attackers of finding a way to penetrate the company and initiate a non-tolerable event.
In the fall of 2022, as a result of an attack on the electricity company of Ghana (ECG), customers of the country's largest electricity supplier were unable to purchase electricity. Some residents experienced power outages for several days due to the disruption of certain systems.
Successful cyberattacks can cause power outages in entire areas. For example, earlier in 2021, an attack on the electricity supplier Ghana Grid Company Limited (GRIDCo) in West Africa left residents of Ghana without electricity for 5 days.
Who is attacking Africa, and how
Targets and methods of attacks
In attacks on organizations, criminals most often target computers, servers, and network equipment (85%). Web resources are targeted in 15% of attacks; typically, in these cases, attackers managed to successfully carry out DDoS attacks.
Attackers used malware in 4 out of every 5 successful attacks on organizations. Every second incident (52%) involved social engineering. In 37% of successful attacks, vulnerabilities were exploited, and in each tenth case, attackers were able to gain access to organization's resources by compromising credentials.
In attacks on individuals, the most popular method remains social engineering (91%), along with the use of various types of malware (45%). In 9% of successful attacks, cybercriminals managed to compromise the supply chain. For example, the Lemon Group discovered by Trend Micro researchers infected over 9 million Android devices to conduct fraudulent activities. Experts believe that in this case, the attackers managed to compromise the software supply chain.
Malware
Most often, several types of malware were used in a single attack. The most common are malicious remote access tools (RATs, 54% in attacks on organizations), ransomware (33%), loaders (31%), and spyware (27%).
In attacks on organizations, the attackers mainly distributed malware via email messages containing malicious attachments. Systems were also infected with malware when the organization's resources were compromised—for example, by exploiting vulnerabilities in the network perimeter. In the case of private individuals, malware mainly found its way onto their devices through fraudulent websites, emails, and social networks.
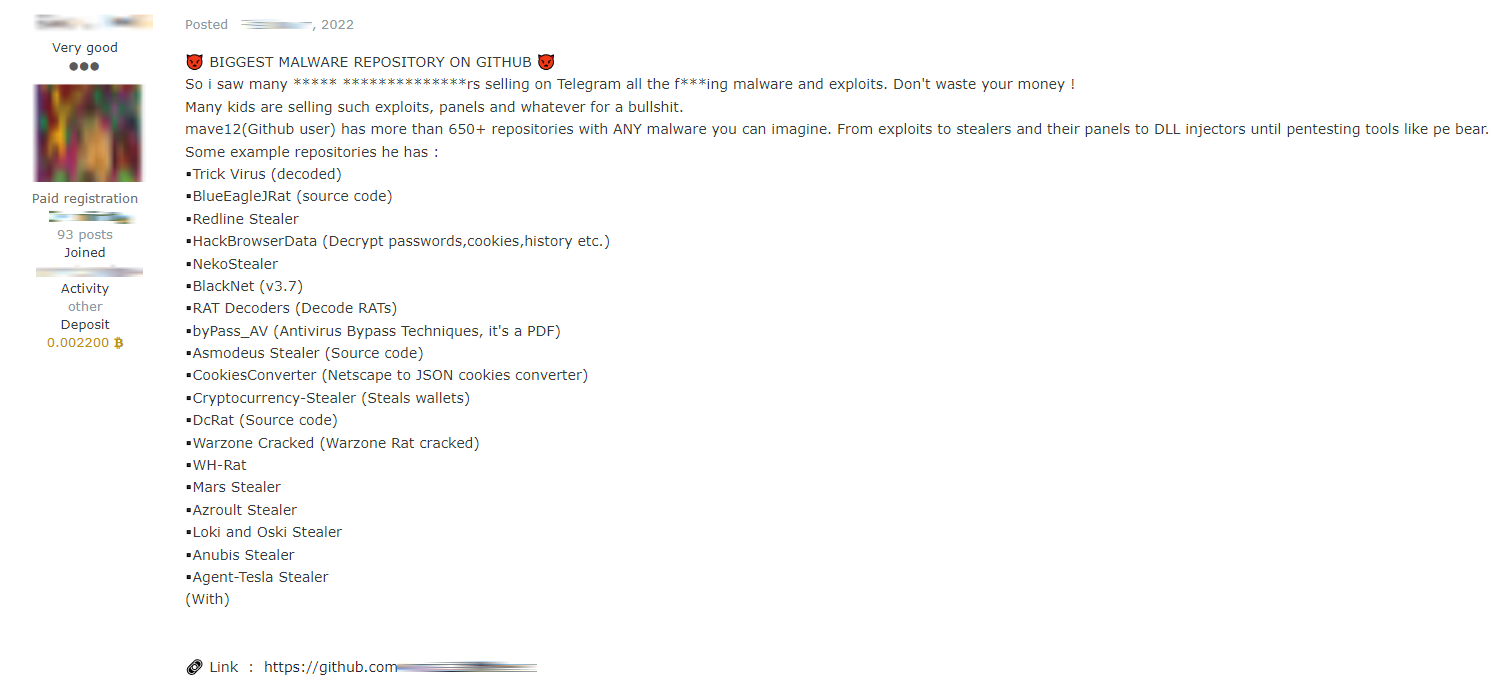
The popularity of attacks using malware in Africa is also influenced by the fact that on the dark web, malware is actively sold and, in some cases, even provided free of charge by cybercriminals. For example, one of the ads offered for sale the Hive ransomware used in an attack on the Bank of Zambia in May 2022.
Another remote-control malware known as Venom RAT can be rented for a month or a year. For an annual license, the criminals charge USD 1,550, while using the malware for a month costs USD 350. Posts offering free access to the source code of various malware families, including the remote access trojan named BlackNET, were also found. Note that the malware mentioned above was used by the OPERA1ER group. The attackers usually gained initial access through phishing emails, after which they deployed a wide range of malware, including Netwire, BitRAT, AgentTesla, Remcos, Neutrino.
Ransomware
A third of attacks using malware aimed at organizations involved ransomware. The most frequent victims were trading companies (25%), followed by the industrial sector (19%) and financial organizations (13%).
The most common method of distributing ransomware is through compromising computers, servers, and network equipment (74%). This indicates the low security of companies, namely vulnerabilities in the network perimeter and сonfiguration flaws in externally available services. Note that ransomware operators often purchase the credentials of compromised companies from access brokers.
Cyberespionage and data leaks
In successful attacks on organizations, attackers aimed to steal personal data (28% of stolen information), trade secrets (26%), and credentials (23%). Confidential information was most often stolen from financial and trade organizations.
In attacks on individuals, credentials (40%), personal data (27%), and payment information (13%) were the types of data most frequently compromised.
In a number of attacks, the attackers stole confidential information as part of a cyberespionage campaign. The attackers are also active on the dark web, sharing databases of employees and customers of companies. These archives contain such personal data as full names, addresses, phone numbers, and email addresses.
For example, at the beginning of 2023, cybercriminals made the database of Ahmed Ben Bella University (Oran 1) students publicly available. The data included the email addresses, names, phone numbers and addresses of more than 50,000 students.

Cybercriminals also offer data for sale. The obtained information is used for fraud and in cyberespionage campaigns. For example, one posting advertised a database of email addresses of employees of the Nigerian Ministry of Justice. According to the cybercriminals, this information can be used for phishing attacks, malware distribution, or for espionage.
The African region is regularly targeted by various groups. Multistage, well-planned, and well-organized attacks targeting a specific industry or (usually a major) company are called advanced persistent threats (APTs). To conduct such attacks, hackers form criminal groups, known as APT groups. The main objective of the majority of these groups is espionage. Let's look at some of these groups, whose activities were observed in African countries:
- Witchetty. This group, also known as LookingFrog, TA410, Cicada, and APT10, focuses its attacks on government institutions, financial organizations, industrial companies, charitable organizations and representatives of diplomatic missions in the Middle East and Africa.
- Mustang Panda. A Chinese group, also known as TA416, RedDelta, or BRONZE PRESIDENT. Targets government institutions and religious organizations in the United States, Africa, Europe, Mongolia, Myanmar, Pakistan, and Vietnam.
- Daggerfly. This group, also known as Evasive Panda or Bronze Highland, attacked an African telecommunications company and engaged in espionage campaigns against representatives of international non-governmental organizations in China and Nigeria. The most commonly used tool in their attacks is the remote access trojan named MgBot.
- Alloy Taurus. This Chinese cyberespionage group (also known as Gallium or Softcell) is focused on telecommunications companies and military and government agencies in Afghanistan, Australia, Belgium, Cambodia, Malaysia, Mozambique, the Philippines, Russia, and Vietnam.
- MuddyWater. This Iranian cyberespionage group (also known as Earth Vetala, MERCURY, Static Kitten, Seedworm, or TEMP Zagros) has been targeting government agencies, including local authorities, telecommunications companies, defense industry enterprises, media, scientific and educational institutions, and oil & gas companies in the Middle East, Asia, Africa, Europe and North America since 2017.
DDoS attacks
DDoS attacks are also one of the most common threats, with government and financial institutions in Africa regularly targeted. For example, in early May 2023, a group of cybercriminals known as Mysterious Team Bangladesh The Bangladeshi cybercriminal group Mysterious Team Bangladesh is focused on government institutions and media outlets. Their primary motivation is hacktivism. Mostly, these cybercriminals target web resources, conducting DDoS attacks and defacing websites. carried out a series of DDoS attacks on Ethiopian institutions. Among the victims were government agencies, an electricity industry enterprise, the Ethiopian government's portal, the Ministry of Health and a private commercial cooperative bank. The group later successfully attacked institutions in Senegal.
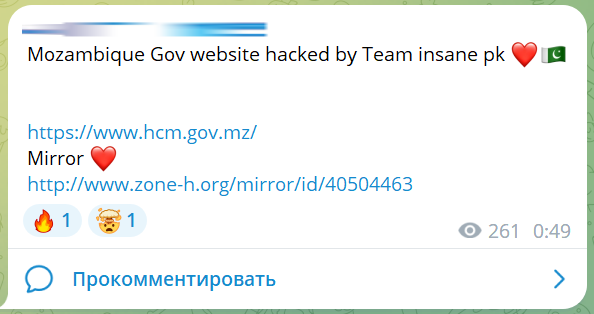
In early February, another group, Team_insane_pk The cybercriminal group Team_insane_pk focuses its attacks on government institutions and high-ranking citizens in Africa, Israel, India, and Australia. The perpetrators select their targets based on religious and political beliefs. They primarily carry out DDoS attacks and website defacements. attacked the website of the Maputo Central Hospital (Hospital Central de Maputo in Mozambique).
In June, an entire DDoS campaign was discovered targeting financial and government institutions in Uganda. Among the victims were the Bank of Uganda, the stock exchange, the parliament, as well as many ministries.
Social engineering
Social engineering attacks are one of the primary cyberthreats to organizations and individuals both worldwide and in the African region. For example, in South Africa in 2022, 94% of organizations experienced phishing attempts. Interpol also includes social engineering in the list of the main threats in the region. Attackers use a variety of social engineering tactics, automated tools, and spam bots to maximize their chances of success. Aggravated by poor cybersecurity awareness among users, the risks associated with phishing attacks remain exceptionally high. According to assessments of employee awareness in African companies conducted by KnowBe4 researchers, one in every three employees clicks on a phishing link or otherwise does what the attackers request.
According to our data, social engineering is used in 52% of successful attacks on organizations and 91% of attacks on individuals in the African region. For organizations, the most common type of phishing attack is sending emails with malicious links or attachments. In 29% of cases, fake sites are used that may imitate, for example, corporate authentication pages, well-known banks, or payment systems. The availability of ready-made phishing tools and services on the dark web makes things much easier for attackers, allowing even those without technical knowledge to quickly create deceptive mail campaigns and fraudulent websites.
The financial sector is the most frequent target of phishing attacks. In 2022, Check Point Research discovered a malicious campaign called DangerousSavanna that targeted medium and large financial institutions in French-speaking Africa and was active for at least two years. The attackers sent emails with malicious attachments to employees of financial institutions in Ivory Coast, Morocco, Cameroon, Senegal, and Togo. To make the emails appear genuine, the attackers used domain addresses that closely resembled the addresses of other well-known African financial institutions, such as the Tunisian Foreign Bank, and in recent attacks they replaced the sender's email address with the address of a local insurance company.
Individuals mostly become victims of phishing attacks by visiting fraudulent websites or encountering cybercriminals on social networks and instant messengers.
Business email compromise
Another type of attack that uses social engineering methods is business email compromise (BEC). In this attack, criminals gain access to an email account of an organization's employee and use it for their own purposes—usually fraud or theft of money or data. For example, the attacker may intervene in correspondence with a partner company and send new banking details for a transfer, or impersonate the head of the organization and instruct the accounting department to make a payment to a certain account.
The damage from a BEC attack can run into millions of dollars. Thus, according to the FBI, US companies suffered losses amounting to USD 2.7 billion in 2022 (exceeding losses from ransomware attacks), and this amount is growing every year.
The African region is experiencing a significant increase in BEC attacks. Attackers usually pose as senior executives, government officials or business partners to deceive their victims. Both small and large organizations are targeted. The great danger of BEC attacks lies in the fact that the attackers are well acquainted with the particularities of the region: more than half of BEC groups are located in Africa. According to Unit42 researchers, one of the largest cybercriminal communities carrying out BEC attacks is located in Nigeria. Businesses in Africa are increasingly being targeted by international BEC groups and attacks are being carried out from various countries, mainly Nigeria, Ghana, and South Africa.
Although members of BEC groups are relatively easy to identify and the movement of funds can be traced (unlike ransomware groups, for example), many factors make it difficult for law enforcement agencies to apprehend the criminals. These include the territorial distribution of criminal groups, the international nature of cyberattacks, delayed detection of attacks, and the lack of unified incident notification mechanisms.
Sale of access on underground forums
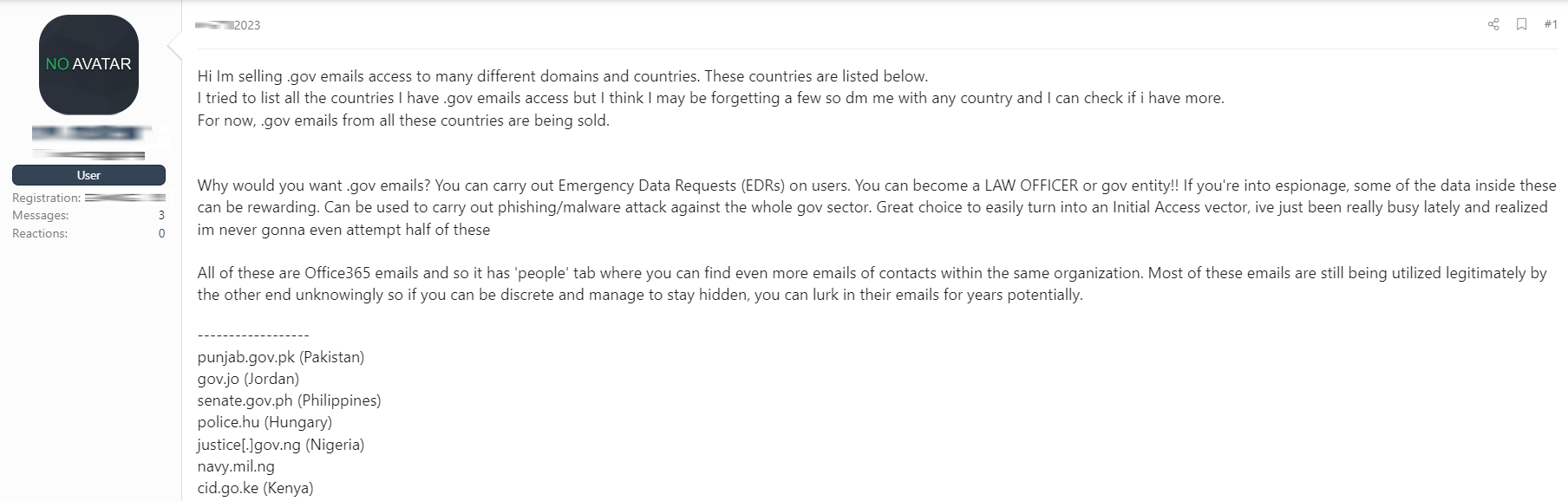
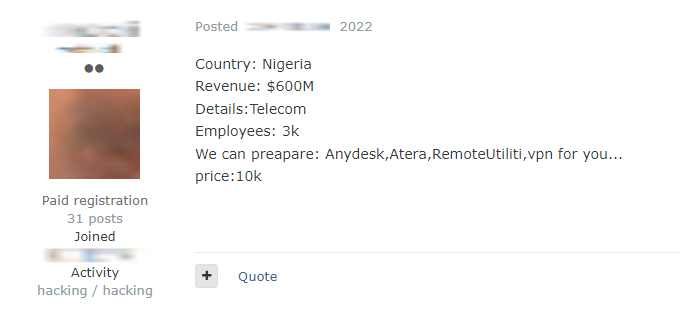
According to our data, cybercriminals are actively using underground forums to buy and sell access to the networks of major African companies, including government and financial institutions, trade enterprises, and IT companies.
The average cost of access with domain administrator privileges is about USD 300, while access with local administrator privileges is cheaper, costing USD 170 on average. Among all the ads found, the largest price requested was USD 10,000 for connecting to the infrastructure of a Nigerian telecommunications company.
Attackers on underground forums are also actively looking for African "drops"—individuals who participate in fraudulent schemes for illicit income. For example, requests for drops in Nigeria, Senegal, Algeria, and South Africa were found in Telegram channels.

Conclusions and recommendations
Africa is a large region with uneven distribution of resources among countries, a region that continues to face numerous socio-economic challenges. However, in recent years the continent has emerged as a fast-growing digital giant, thanks to ongoing reforms. Organizations are building infrastructure and providing services to enable digitalization at a rapid pace, but the introduction of new technologies is also opening up new opportunities for cybercriminals.
Below we propose a range of measures aimed at improving the cybersecurity of individual organizations, industries, and the African region as a whole.
Recommendations for governments
Adopt information security policies and strategies at a national level
Governments should develop, implement and regularly update national cybersecurity policies and strategies, involving a wide range of stakeholders in the process. The process of developing these strategies should have the necessary funding and political support to ensure effective coordination and a clear allocation of responsibilities.
The national information security strategy should include assessment of threats, as well as well-defined goals and the steps required to achieve them. Representatives of government organizations, business, and the cybersecurity sector should be involved in the development process, and draft strategies should be considered and discussed publicly.
The strategy must also be regularly reviewed and updated to ensure that its content stays relevant for current threats.
Develop legislation for personal data protection
Governments should work on creating and implementing legislation for the protection of personal data. This legislation should combat cybercrime, guarantee the protection of personal data, and maintain the digital security of citizens and organizations. It should also facilitate effective coordination between different law enforcement and security agencies. Additionally, mechanisms for international cooperation should be established to more effectively catch and prosecute cybercriminals and share information on international cyberthreats.
Protect critical information infrastructure
Governments should identify critical information infrastructure, disruption of which could cause non-tolerable events at the level of industries and countries. This approach helps to effectively allocate resources to ensure the protection of the most critical systems. Priority should be given to the infrastructure of sectors such as government, telecommunications, and finance, as well as other industries vital to the economy and national security, such as agriculture, mining, or manufacturing. The speed of digital transformation in the country and the maturity level of information security should also be taken into account.
The security of critical infrastructure is often dependent on external ICT providers. Governments should ensure the protection of power supply networks and Internet access points, diversify the range of providers of key technology infrastructure, and encourage the development of African enterprises capable of supplying, maintaining and protecting critical information infrastructure.
Create national and industry cyberincident response centers
Establishing national cyberincident response teams (CIRTs) to monitor threats and help organizations recover from major cyberattacks should be a top priority for governments. At the time of writing this report, only 26 African countries have national CIRTs. Countries where such structures already exist should establish sectoral CIRTs and collaborate to support the creation of regional and continental CIRTs. It is necessary to develop clear and transparent mechanisms for reporting cyberincidents occurring in organizations. Responding to cyberthreats must be integrated into the overall strategy for protecting and restoring critical national infrastructure.
Cooperate internationally
Support for regional and international efforts to combat organized cybercrime is essential. Attempting to fight cybercrime exclusively within regional borders is in most cases futile. Governments must adopt policies, procedures and agreements that enable them to collect and share digital evidence and extradite cybercriminals. Increasing international collaboration will help African countries to stay informed about the latest cyberthreats, cooperate with other nations in the fight against cybercrime, and contribute to the development of global cybersecurity norms and policies. Active participation in these efforts will empower African governments to better protect their countries, citizens and critical infrastructure from cyberthreats.
Recommendations for businesses
Identify non-tolerable events and critical assets
To ensure the cyber-resilience of a company, it is necessary first of all to analyze the main risks and draw up a list of non-tolerable events that could cause significant damage to its activities. This step will help identify critical assets and focus on protecting the most valuable resources. A strategy should be developed to prevent non-tolerable events, including the necessary security measures and monitoring of network activity using modern security tools.
Monitor incidents and respond to cyberthreats
Incident monitoring and detection systems are needed to respond to potential threats and attacks in a timely manner. For this purpose, we recommend using SIEM systems that collect and analyze information about security events from various sources in real time. Together with XDR (extended threat detection and response) and NTA (network traffic analysis) solutions, this will help detect attacks in the early stages and ensure swift responses, reducing risks for your organization.
Evaluate cybersecurity effectiveness
The effectiveness of adopted cybersecurity measures should be regularly tested to assess the performance of the strategy and defenses. We recommend paying special attention to verification of the events non-tolerable for the organization.
It is also worth considering participating in bug bounty programs so that external security researchers can find new vulnerabilities. This will help detect and eliminate vulnerabilities before attackers can exploit them.
Train employees and develop information security specialists
It is essential to educate employees about cybersecurity and conduct training sessions to increase awareness of current cyberthreats and protect against social engineering techniques.
To effectively combat cyberthreats, African organizations should invest in the development of their cybersecurity experts. Regular training and certification of cybersecurity employees will enhance their skills and knowledge, boosting the company with expert support in preventing and responding to cyberattacks. One of the most effective ways to do this is to participate in cyberexercises on dedicated platforms, where information security specialists can practice recognizing attack techniques and countering them.
About the research
This report contains information about infosec incidents in the African region, based on Positive Technologies' own expertise, study findings, and data from reputable sources.
We believe that the majority of cyberattacks are not made public due to reputational risks. Consequently, even organizations that investigate incidents and analyze hacker activity are unable to do a precise count of threats. Our research aims to draw the attention of companies and individuals who care about the state of information security to the key motives and methods of cyberattacks, highlighting the main trends in the changing cyberthreat landscape.
This report considers each mass attack (for example, phishing emails sent to multiple addresses) as one incident, not several. For explanations of terms used in this report, please refer to the Positive Technologies glossary.
