Contents
- Executive summary
- Statistics
- Attack consequences
- Malware: seasonal updates
- Ransomware: new approaches and a fresh angle
- APT groups: the power of tactics
- Social engineering: the power of words
- Attacks on government: a tale of two encryptors
- Attacks on industry: tilting at windmills
- Attacks on transportation: up in the air
- About the research
Executive summary
- Compared to Q1 2022, the number of attacks in Q2 fell by 2%. Targeted attacks accounted for 71%.
- The share of attacks against individuals was 17%. We saw an increase in the use of spyware in attacks against individuals (41%) and the use of phishing sites in attacks involving social engineering (43%).
- Most often, attacks on companies resulted in disruption of core business (50%) and leakage of confidential information (40%). Individuals were victims of confidential information leakage in 69% of attacks, and suffered financial losses in one in three attacks.
- The number of attacks on organizations' web resources continues to rise: 28% in Q2, up 6 percentage points on the previous quarter.
- There was an increase in ransomware activity: almost a third of attacks in the entire quarter involved ransomware, while the share of ransomware among other types of malware was 62%, which is similar to the figure in late 2021. Groups are developing new ways to pressure victims, adding new features to malware and even launching bug-bounty programs.
- The number of attacks by APT groups broke the previous record, set in Q4 2021. Spyware groups used ransomware to divert attention from their core activity, employed techniques and malware similar to those used by other groups, and even hunted each other.
- Cybercriminals exploit the popularity of cryptocurrencies in attacks based on social engineering to steal credentials and money, as well as distribute malware disguised as free NFT tokens. There was an overall increase in the number of attacks on blockchain projects compared to 2021.
- Government agencies again faced the highest number of cyberattacks. Most often, attacks led to disruption of core activity, as well as leakage of confidential information. In 46% of cases, government agencies were attacked using malware, of which 63% was ransomware; some victims were forced to pay a ransom.
- We note a significant increase in the number of attacks on companies in the industrial sector, up 53% against the previous quarter. In most cases, these attacks led to disruption of industrial operations (53%) and leakage of confidential information (55%).
- Q2 saw a significant rise in the number of attacks on transport companies: almost double the figure posted in Q1 2022. The most high-profile attacks affected the aviation business.
To protect against cyberattacks, we first and foremost recommend following our general guidelines on personal and corporate cybersecurity. We advise keeping all software up to date and installing security updates. Companies and organizations should adhere to the regulatory guidelines and recommendations on updating foreign-made software, and monitor changes in legislation. In addition, employees should be kept informed of all the latest phishing techniques and scams. Individuals are advised not to download software from suspicious sites and torrents, but to use licensed versions from trusted sources. You can strengthen the security of web resources on the corporate perimeter using modern security tools (for example, application layer firewalls, WAFs). To prevent malware infection, we recommend using sandboxes that analyze file behavior in a virtual environment and detect malicious activity, and paying attention to the permissions requested by downloaded software. Making regular backups can greatly mitigate the effects of attacks by allowing you to restore systems quickly.
Statistics
In Q2 2022, the number of attacks remained at the Q1 level. This is due to the ongoing confrontation in cyberspace and the resumption of ransomware activity. Government, science and education, and companies in the industrial sector were most frequently hit by cyberattacks. There was a noticeable rise in attacks on transportation.
The reporting period witnessed large-scale attacks on web resources by organized groups of hacktivists. Cybercriminals are making more use of phishing and torrent sites to distribute malware.
17% of attacks were aimed at individuals
71% of attacks were targeted
Attack consequences
The slight decrease in the total number of cyberattacks compared to Q1 did not affect the severity of their impact: network infrastructure downtime hit corporate profits, and customers were unable to access services; large-scale DDoS attacks made it difficult or impossible to access web resources; companies in the industrial sector experienced disruption of operations. In addition, cybercriminals gained access to victims' confidential information.
Loss of access and service interruptions
More than two-thirds of attacks that disrupted core business resulted in loss of access to infrastructure or data. Ransomware was largely to blame, which impacted the smooth operation of systems. For instance, a ransomware attack on Greenland's healthcare system almost completely paralyzed medical institutions across the island.
Coordinated attacks caused prolonged downtime, as was the case with Lithuanian and Norwegian government agencies in June (for more detailed attack statistics for government agencies, see below). And in May, following a major DDoS attack on Russia's Unified State Automated Information System (EGAIS) portal, manufacturers and distributors of beverages found themselves unable to send and receive alcohol products.
Information leakage
More than a third of attacks (40%) on organizations in Q2 resulted in leakage of confidential information, slightly less than in the previous quarter. The most frequently stolen information was personal data (36%) and intellectual property (11%). Individuals were more likely to have credentials and personal data stolen, accounting for 41% and 24%, respectively.
High-profile confidential data breaches in Q2 included the attack on Baptist Health Medical Group, which affected more than a million people and compromised personal and medical data, and the hacking of Malaysia's National Registration Department, which resulted in the theft (and sale on darknet forums) of unique IDs, photographs, and phone numbers of more than 22 million citizens of the country. Such leaks put countless people at risk of having their digital identities faked and unlawful actions being carried out in their name. No less attractive to attackers are credentials of organizations and individuals (9% and 41%, respectively) that can be used to attack corporate networks or private accounts: emails published by a former member of the LAPSUS$ group only confirm how easy it is to acquire stolen credentials and how serious the consequences can be. They show that the group often gained initial access to corporate networks of interest simply by buying employee credentials on forums; and during an attack on T-Mobile the cybercriminals managed to access Slack corporate acсounts and repositories with source codes of applications.
Malware: seasonal updates
In Q2, we noted a rise in the number of malware attacks: the share of such attacks on organizations was 57%, and on individuals 59%, which represents an increase of 12 and 13 percentage points, respectively, against the previous quarter. Ransomware became more active: the share of ransomware attacks on organizations increased quarter-on-quarter by 18 percentage points, amounting to 62%. As in the previous quarter, cybercriminals continued to use data wipers in attacks on institutions. In attacks on individuals, we note the prevalence of spyware and banking trojans (41% and 21% of malware attacks, respectively).
New arrival
Researchers at ThreatFabric discovered the new Octo banking trojan, targeting users of Android online banking apps. The new trojan allows attackers to gain remote access to the device screen in streaming mode and execute commands through an overlay on top of the screen. Revive, a piece of spyware adapted as a banking trojan, had similar functionality, as explained by Cleafy researchers in their report. Both trojans have full control over the device and can intercept two-factor authentication codes, which enables on-device fraud—the stealthiest and most dangerous kind of subterfuge, whereby the attacker makes transactions from the same device that the victim uses on a regular basis. This complicates the task of anti-fraud solutions, as there are much fewer suspicious signs.
Due to advancements in user protection and attack detection tools, cybercriminals are having to create and deploy more sophisticated malware and persistence techniques.
Admired by infosec professionals and cybercriminals alike, the post-exploitation tool Cobalt Strike may eventually be replaced by a more recent variant called Brute Ratel. Researchers at Unit42 reported its use in APT29 attacks, adding that many security tools do not detect it as a threat on first detection.
Malware persistence is becoming harder as OS security improves. However, there are ways to remain undetected in the target system, one of which is through bootkits A bootkit is malicious code that runs before the OS boots. The main goal of a bootkit is to gain a foothold in the system and shield other malware from detection by security tools. . These allow malware to run before the OS boots, allowing it to bypass defenses. In Q2, Lenovo devices found themselves at risk of bootkit attacks. The manufacturer installed insecure firmware versions containing vulnerabilities that could be used to disable secure boot and protection features, and execute arbitrary code. Access to BIOS and UEFI was also of interest to the Conti Now discontinued (see the «Ransomware: new approaches and a fresh angle» section below). group, as revealed by Eclypsium. Conti's activity in H1 2022 was aimed at identifying vulnerabilities in the Intel Management Engine microcontroller, which has privileges over the OS and can be used to modify the BIOS (UEFI) flash memory, execute arbitrary code, and even modify the OS kernel in system management mode (SMM). These actions provided near unlimited opportunities to carry out attacks and achieve persistence in the system.
To learn more about bootkits and ways to detect them,
see our report
Dedicated to pirated software lovers
As in the previous quarter, malware distributed via email had a dominant share. Security researchers discovered a massive campaign to spread the new META malware, an enhanced version of the popular RedLine infostealer. Users received an email with a bait document and a text prompting them to open it and run the macro. When macro was enabled in the malicious document, the malware loaded itself into the system and stole credentials stored in the browser.
In attacks on individuals, we noticed an increase in the proportion of malware delivered through websites, including torrents: this method had a 45% share, which is 9 percentage points above the 2021 average.
FFDroider malware was detected on various sites, distributed under the guise of programs for accessing licensed versions of software without purchasing a subscription, as well as freeware. When installed, FFDroider disguised itself as a desktop version of Telegram and accessed browsers, retrieving cookies and hash sums of passwords for Twitter, Facebook, and Instagram. Using the Windows CryptoAPI service, the stealer decrypted the passwords and sent them, together with the cookies, to the attackers' C2 server.
Researchers at Zscaler uncovered several domains mimicking the official Microsoft Windows download page and distributing an ISO image of the operating system with a backdoor; in several cases, the cybercriminals distributed backdoor versions of Adobe Photoshop via Github repositories. The images weighed more than 300 MB, which allowed the attackers to bypass some antivirus products; after running the image, the Vidar infostealer was installed in the system, communicating with C2 through Telegram.
Cross-platforming: the be-all and end-all
In our analytical reports ([1], [2], [3]), we noted the prevalence of Unix systems and their appeal to cybercriminals looking to create (and adapt) their own malicious programs for them.
Corporate virtualization servers make especially attractive targets for cybercriminals. They can run multiple virtual machines, all of which get encrypted during an attack, while the server's computing resources only accelerate the encryption process. Having been ported to Linux in Q2, Black Basta, a strong new ransomware player, has already been used in attacks against VMware ESXi servers. Analysis of the ported version found that it targets the folder containing all virtual machines on the server, and deploys multithreading to hide its tracks and speed up encryption, as well as a utility to gain full access rights to target files.
At the start of Q3 2021, we reported the first recorded use of Windows Subsystem for Linux (WSL) to deliver malware; as of Q2 2022, Black Lotus researchers had detected more than 100 malware variants targeting WSL, which shows an impressive rate of development for a relatively new attack vector. Also discovered was a RAT sample that used Telegram to communicate with C2 and boasted a wide range of features: stealing browser cookies, downloading files, and remotely executing commands. Attackers can use WSL to target both Linux and Windows. Add in the low antivirus detection rates, and this vector looks very promising for them.
Ransomware: new approaches and a fresh angle
Ransomware activity in Q2 increased 1.7-fold against the previous quarter to roughly the same level as at the end of last year. Almost a third of all attacks in Q2 involved ransomware.
Because ransomware distributors exploit current vulnerabilities, the share of ransomware spread via email had been falling up to and including Q1 2022. In Q1, its share decreased by 22 percentage points relative to Q4 2021, while the share of devices compromised through software vulnerabilities increased by 28 percentage points. In Q2, however, the share of email-distributed ransomware returned to mid-2021 levels, partly due to exploitation of the Follina vulnerability, which requires delivery of a bait document by email.
There were noticeable changes in the distribution of ransomware victims by industry: the number of attacks on healthcare facilities dropped by 5 percentage points against the previous quarter, while companies in the industrial sector experienced the highest number of ransomware attacks (17% versus 14% in the previous quarter). The ransomware attacks on government agencies continue unabated.
Pride of place
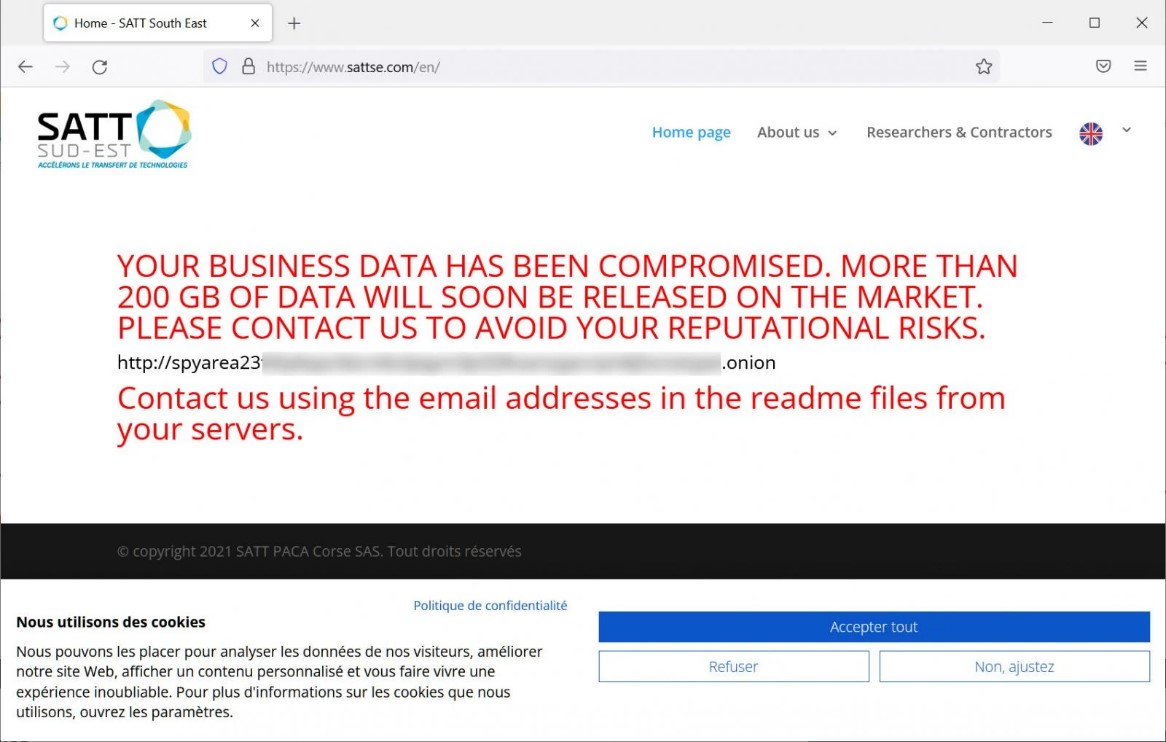
Ransomwarers are constanly on the lookout for ways to draw attention to their attacks. The newly emerged ransomware group Industrial Spy uses a novel way of applying pressure to corporate victims: website defacement. After encrypting files, Industrial Spy penetrates the target website and replaces the main page contents with a ransom note with the group's contact details. One of the first victims of this method was the French company SATT Sud-Est.
The BlackCat group also showed ingenuity in pressuring victims by hosting a site on the clear web allowing employees of attacked organizations to check whether their personal data was stolen.
Faster, stronger
Q2 saw several ransomware groups (Chaos, DeadBolt, ech0raix, Hive, Cuba Ransomware, LockBit) switch to more advanced and effective versions of malware. One of them, Cuba Ransomware, unveiled a new version of its ransomware after a short pause in operations. The developers optimized their creation, adding safelisted directories and file extensions to avoid crashing the system and harming encrypted information, and expanding the list of programs to be terminated during the encryption process, thus allowing encryption of files that were previously in use by these programs' processes, for example, Outlook, MySQL, and others. A link to the qTox chat client was also added for secure, real-time negotiations with ransomware victims and technical support for them.
Weak spots
Not only victims have vulnerabilities, but attackers too. A team of application security researchers found that such well-known ransomware strains as Conti, LockBit, and Black Basta are susceptible to DLL spoofing. This vulnerability affects Windows-based systems and works by allowing a DLL library to be side-loaded from outside the current folder leading to arbitrary code execution or privilege escalation. Exploiting the vulnerability makes it possible to terminate the ransomware just before the encryption process. This requires a specially compiled DLL file with the exploit code to be placed in folders likely to be used by the attackers. At the same time, note that exploiting a vulnerability does not prevent data theft from the compromised system, which can be the cybercriminals' target; for example, the Karakurt group demands a ransom for not disclosing stolen data without encrypting it.
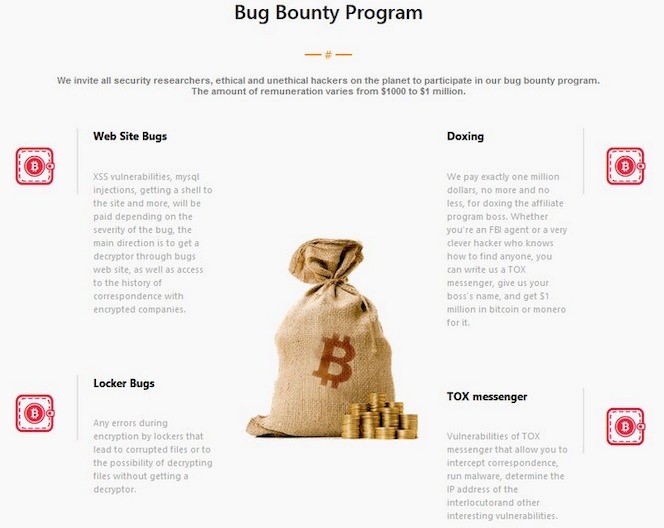
Cases like these pose additional challenges for malware developers to find vulnerabilities and to improve the reliability of their programs. Legitimate vendors have bug bounty programs, in which researchers search for vulnerabilities in applications and receive a monetary reward for finding any. Among cybercriminals, the scheme is being pioneered by the LockBit group, which announced a new version of its malware and the first ransomware bug bounty program.
Notable attacks in Q2
In Q2 2022, the most active ransomware was:
- LockBit
- Conti The group announced the end of operations and shut down its servers and data leaks site on May 19, 2022.
- BlackCat AKA ALPHV
- Black Basta A new ransomware group, whose first attacks were recorded in April 2022.
- Hive
Early in the quarter, we saw an attack by the new, but formidable Black Basta ransomware group, which caused a massive failure in the IT infrastructure of the German wind turbine manufacturer Deutsche Windtechnik and paralyzed its online resources. Black Basta also attacked the American Dental Association, forcing a shutdown of affected systems and leaking masses of personal data and corporate information.
In May, SpiceJet Airlines was hit by a ransomware attack that left employees and passengers in trouble. A prolonged IT system outage caused flight delays and cancellations; airline staff had to manually check in passengers as the reservation service was down.
The Vice Society ransomware group claimed responsibility for the June attack on the administration of the city of Palermo in Italy. The attack caused a blackout of all public systems in Palermo, including government agencies, police stations, and video surveillance; tourists and locals were unable to pay for transport or buy tickets for cultural and sporting events.
APT groups: the power of tactics
Throughout 2021 we saw a rise in the activity of APT groups worldwide; in Q2 2022 we recorded another uptick in the number of attacks emanating from highly skilled and disciplined groups. Combining own malware developments, out-of-the-box techniques, and previously unknown vulnerabilities, APT groups are able to compromise corporate networks and devices, remaining undetected for a long time. A well-planned APT attack is not easy to detect. Many successful attacks go unnoticed for some considerable time. We recommend that all organizations check their security measures for resistance to APT attacks.
Diversionary tactics
APT groups' primary aims are long-term persistence in the victim's network infrastructure, in-depth reconnaissance, and collection of as much sensitive data as possible. Ransomware has become one way of diverting attention from the true purpose of the attack. For example, researchers at Secureworks concluded that groups such as APT41 and APT10 used ransomware as a distraction in their attacks. Once inside the victim's system, the loader disabled protection mechanisms and downloaded LockFile, Rook, Pandora, and Night Sky ransomware. Downloaded at the same time were the remote access tools Cobalt Strike and PlugX, which made it possible to gain a foothold in the system and exfiltrate data. Given that these encryptors shared code sections and had similar C2 infrastructure to the above-mentioned APT groups, we can conclude that the cybercriminals' motives were not financial, but spy-related, and these tools were used to divert attention from the main goal of cyberespionage.
Throwing the bait
Besides their wide-ranging malware, APT groups use various socio-technical methods—such methods were used in 76% of attacks in Q2.
Known for its attacks that exploit the human factor, the Lazarus group once again turned to social engineering: in Q2, the group continued its operation to spy on employees looking for better job opportunities. Users received "job offers" via email with malicious links or attachments. Clicking or opening them caused spyware to be installed.
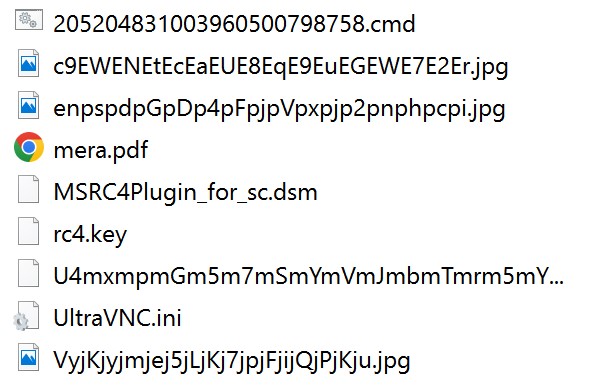
In Q2, PT Expert Security Center (PT ESC) discovered PseudoGamaredon, a group of cybercriminals copying the tools, tactics, and techniques of the Gamaredon APT group: use of geopolitical topics, distribution of malicious attachments via email, and use of SFX archives with the double extension .doc.exe. Both groups made use of legitimate UltraVNC remote access software, the difference being that the "real" Gamaredon used documents with malicious macros to gain initial access to compromised devices, or employed Template Injection techniques.
To catch the robbers, target the ringleader
APT groups keep their own data under lock and key, and never willingly reveal information about members and network infrastructure. Disclosure of such information can have serious consequences, up to prosecution in many countries.
In Q2 2022, the BlueHornet group was found to be pursuing a rather unusual goal: to reveal details of other APT groups and their infrastructure. In an interview, BlueHornet said it had managed to get hold of information about members of such well-known groups as APT28, APT40, and Lazarus, including personal data, credentials, and even current location. All the collected information was posted on the RaidForums RaidForums was shut down as a result of Operation TOURNIQUET, during which Europol seized the illegal marketplace's infrastructure and arrested the forum administrator and two accomplices. platform, and, judging by the number of hits, was much sought-after.
Social engineering: the power of words
Social engineering was the most common method for attacking individuals and the second most for attacking organizations in Q2 2022: 93% and 43% of attacks on individuals and organizations, respectively, exploited the human factor. Cybercriminals use a variety of ways to influence people through social engineering, which, if successful, can result in theft of confidential information, delivery of malware, and major financial losses.
Big-game phishing
The most widespread social engineering vector in attacks on organizations was email: through phishing campaigns, malefactors stole user credentials and penetrated corporate systems. According to law enforcement agencies, known losses due to business email compromise (BEC) since 2016 amount to $43 billion. Under the guise of legitimate money transfer requests, cybercriminals siphon off money into their own accounts: the City of Portland was recently scammed in this way to the tune of $1.4 million.
Sometimes attackers combine social engineering methods to put more pressure on the victim: Q2 saw attacks on banking app users which began with the receipt of a text message about a "suspicious" transaction on their account. If the victim responded, they got a call supposedly from the bank's support service, who tried to trick them into linking their account to a fraudulent email address, after which the funds there was stolen.
No place for newbies
Cybercriminals make active use of topical news. Cryptocurrency is currently one of the hottest topics, and the number of attacks on blockchain projects and crypto exchanges continues to rise, 27% more in H1 2022 than in the whole of 2021. At the same time, cryptocurrency holders get targeted by intruders looking to steal their virtual savings in ever more artful ways.
Many users already know not to click on links and download attachments from emails from unknown addresses. But what if an email looks legitimate and came from a trusted source? Owners of cold (stored offline) Trezor cryptocurrency wallets were hit by a sophisticated attack in which a seemingly legitimate email prompted them to change their PIN and install backdoor firmware on their device. This happened after the cybercriminals managed to compromise Trezor's mail provider and send out emails in the company's name urging recipients to update the firmware, which caused their wallet credentials to leak.
Attackers continue to use phishing sites: almost half of all socio-technical attacks on individuals in Q2 involved fake sites. Phishers faked the popular Pixelmon NFT site to distribute the Vidar remote access trojan under the guise of free NFT tokens and virtual collectibles.
Not only cryptocurrency users are targeted by cybercriminals. Because developers of DeFi platforms have direct access to the platform code and infrastructure, cybercriminal interest in them is rising, in particular on the part of APT groups, who excel in social engineering and have the skills to figure out how the platform code works. One such attack was carried out by Lazarus Group. Using a malicious file with a juicy job offer, the cybercriminals were able to compromise the device of one of the developers of the DeFi platform Harmony Protocol, steal two sets of private keys, and carry out a $100 million heist.
Attacks on government: a tale of two encryptors
In Q2 2022, government agencies faced the most cyberattacks among organizations; their share of the total number of attacks increased by 2 percentage points, compared to the previous quarter.
59% of cyberattacks on government agencies disrupted their core activities, which in turn can damage the interests of the state (65%).
In April, cybercriminals pulled off an attack on the national postal service of Bulgaria, which affected mail delivery and payment of pensions and benefits, and also gained access to and encrypted the organization's database. Because such incidents harm national prestige and undermine public confidence, the management was forced to resign. City officials in Quincy, Illinois, were under investigation after the mayor admitted spending $650,000 in H1 2022 on a cleanup operation after a ransomware attack.
Almost one in two attacks on government agencies used malware, with ransomware being the most popular among cybercriminals. In an unprecedented attack on government in April, the Conti ransomware group hit Costa Rican government agencies and demanded a ransom of $20 million. With most of the country's IT infrastructure down, a state of emergency was declared. It wasn't long before the Costa Rican healthcare system also came under fire, this time by the Hive group. In addition, PT ESC detected attacks on Russian government agencies by the Tonto group, aimed at installing loaders on compromised systems and harvesting network information by sending out malicious RTF files exploiting a vulnerability in Microsoft Office.
Attacks on industry: tilting at windmills
In Q2 2022, companies in the industrial sector accounted for 13% of attacks on organizations, up 5 percentage points against the previous quarter, while the total number of attacks on organizations in the sector increased by 53%—a consequence of the above-mentioned rise in ransomware activity. The share of malware attacks was 76%, with ransomware (61%) leading the pack.
The number of attacks on companies in the industrial sector increased by 53% compared to Q1 2022
In early April, an attack by the Conti group on wind-turbine giant Nordex encrypted the firm's information infrastructure and caused a major shutdown of remote access to turbines. At roughly the same time, Black Basta penetrated the systems of Deutsche Windtechnik, a specialist company in wind turbine maintenance, stole corporate information, and temporarily disabled around 2,000 wind turbines across Germany.
More than half (53%) of cyberattacks affected the stable operation of companies in the industrial sector. In Q2, an attack by the Gonjeshke Darande group on three Iranian steelworks stood out for disrupting production processes and toppling a ladle holding liquid iron, which caused a fire on the factory floor. The attackers reportedly used data wipers, one of the trends of the previous quarter.
Attacks on transportation: up in the air
The transportation sector has been hit by large-scale attacks since the beginning of the year, with a quarter-on-quarter rise of 82% in the number of attacks in Q2, a consequence of the increase in the amount of coordinated DDoS attacks and ransomware activity. Passenger transport and information services were the main casualties. For instance, a string of major DDoS attacks by Killnet hacktivists took down Czech Railways' web applications, making it impossible to buy and reserve train tickets.
Aviation is at special risk from cyberattacks: this mode of transport is particularly sensitive to delays and disruptions. That same Killnet group attacked Pardubice Airport,again in the Czech Republic, crashing all web services, including the official site. Thousands of passengers had their plans ruined after Sunwing Airlines was hit by an attack on its information systems. According to the airline's CEO, a third-party service provider was compromised, which disrupted the main website and passenger check-in system. It took four days to clean up the consequences.
A major incident occurred in Swiss airspace due to a malfunction in Skyguide's air traffic control system. Problems with the system, in particular a switch failure, led to the suspension of takeoffs and landings at Geneva and Zurich airports, forcing Switzerland to temporarily close its airspace. Skyguide denied a cyberattack, although some reports suggested that ransomware was to blame. Experts have yet to determine the cause of failure.
About the research
This report contains information on current global information security threats based on Positive Technologies' own expertise, investigations, and reputable sources.
We estimate that most cyberattacks are not made public due to reputational risks. As a consequence, even companies specializing in incident investigation and analysis of hacker activity are unable to quantify the precise number of threats. Our research seeks to draw the attention of companies and ordinary individuals who care about the state of information security to the key motives and methods of cyberattacks, as well as to highlight the main trends in the changing cyberthreat landscape.
This report considers each mass attack (for example, phishing emails sent to multiple addresses) as one incident, not several. For explanations of terms used in this report, please refer to the Positive Technologies glossary.
