According to our data, phishing remains one of the main attack vectors of cybercriminals. The number of attacks on individuals using social engineering has significantly increased: in Q3 2020 they accounted for 67%, in the same quarter of 2021 the figure was 83%. Attackers do not stand still and are constantly refining their methods of scamming victims. The volume of attacks keeps growing, and the consequences are becoming ever more serious. Phishing is considered the second leading cause of data leaks. According to IBM, a successful phishing attack costs business an average of $4.65 million.
This report looks at the most common and, in our opinion, interesting phishing topics used throughout 2021.
COVID-19 continued
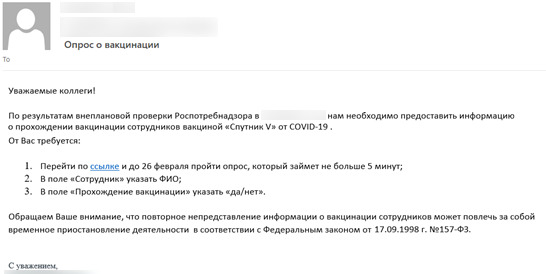
As long as the virus is active and poses a health threat to humans, the pandemic will remain a popular topic among cybercriminals. In 2020 we saw more emails offering information about the coronavirus, treatment methods and plans to return to the office. In 2021, as we expected, the main topic was vaccination. For example, various phishing schemes were related to fake QR codes and vaccination certificates, fake vaccination surveys from pharmaceutical companies and clinics, and the collection of information about vaccinated employees.
Collecting vaccination data
Because the pandemic still has a tremendous impact on all kinds of organizations, coronavirus-themed corporate newsletters are still commonplace. Attackers often disguise their emails as work correspondence, and such methods are often successful, as evidenced by our awareness testing results.
A particularly effective phishing attack scenario is based on employee vaccination polls seemingly sent by HR. In 2021, an average of 65% of employees clicked on the links in such emails, and 48% entered their corporate credentials into a fake authentication form.
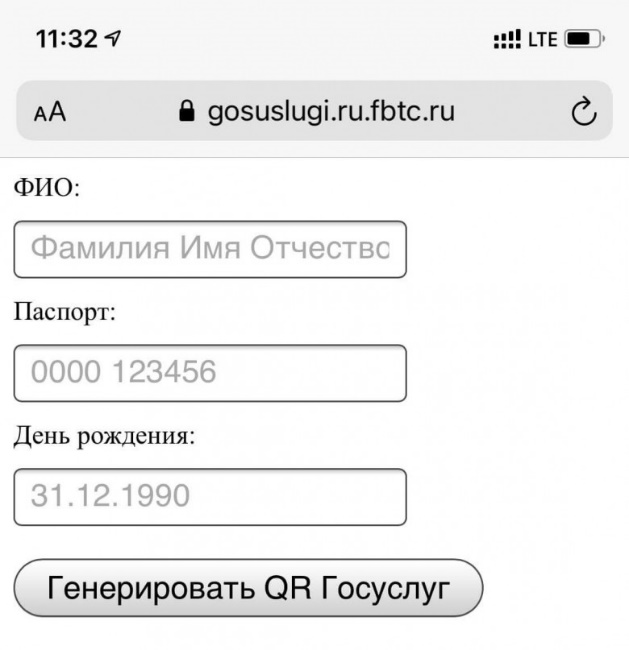
Fake vaccination certificates
Following the introduction of certain benefits for vaccinated citizens in some countries, cybercriminals began selling fake vaccination certificates, with victims being asked to enter their personal data to «generate the certificate.» For instance, as the COVID-19 situation deteriorated in the fall, dozens of fake government websites sprang up, offering visitors fake vaccination QR codes.
Corporate emails
Phishing emails often look like regular messages from partners or other company employees, notifications from services or work tools used in the organization. For example, you might receive notifications from Microsoft products or messages from HR or technical support.
Our work on security analysis has shown the following scenarios to be particularly effective:
- News about salaries and bonuses: on average, 28% of employees opened files containing such information.
- News about social benefits, for example, health insurance programs: on average, 54% of employees opened attachments to such messages.
- News about updated bank charges: 59% of employees on average opened these messages.
In the event of a real attack, these files would contain malware which, if run, could cause unacceptable consequences for the company.
New TV shows and movies
The release of a new TV show or movie always prompts phishing attacks on users of streaming services, such as Netflix. When users enter their credentials on fake sites mimicking popular services, usernames and passwords are immediately stolen. In addition, phishing sites can ask victims to take out a new subscription or renew a current one. If «payment» is made to an attacker, the bank card details fall into cybercriminal hands. Such techniques were used, for example, on the release of a special edition of the show «Friends».
There are other interesting cases linked to the release of popular TV shows. For example, when the famous South Korean TV series «Squid Game» was released, cybercriminals set up fake online stores selling merchandise, distributed malware under the guise of smartphone games, and even printed cards—like those in the series—with QR codes pointing to fake sites.
Sporting events
Attackers continue to exploit major sporting events for phishing purposes. For instance, the FIFA World Cup, due to kick off in November 2022, began figuring as a phishing topic a year ago. Note that phishing emails on this topic mainly contained invitations to bid for contracts to supply goods or services for the tournament.
Also in 2021, phishers took advantage of the Tokyo Olympic Games and the UEFA European Championship. For the latter, besides phishing emails, cybercriminals created fake ticket sites.
Bank customers in the crosshairs
In 2021, numerous fake sites imitating well-known banks were blocked. Exploiting the reputation of popular brands, cybercriminals lure users with the promise of payouts, for example, compensation to fraud victims, offer rewards for taking part in surveys or loans on favorable terms, and steal account credentials when entered.
Attackers may also send emails related to mobile banking issues. Such messages tend to stress the urgency of the problem, counting on the recipient to panic and act in haste, and thus fail to spot inconsistencies in the email, such as a suspicious sender’s address.
Mail services
Another popular phishing topic is emails from delivery services. As a rule, these inform the recipient that a small payment is due for items such as customs fees or shipping charges. The victim who falls into the trap risks losing not only bank card funds, but also personal data.
Another popular scenario involves messages that prompt users to check the delivery status of their shipment by clicking the link in the email. Such links generally point to fraudulent sites.

Travel and vacation: emails and websites offering tickets and bookings
Fraudsters have long been interested in the topic of travel and vacation. Cybercriminals create fake resources where victims can «book» hotel rooms, flights and tours. Links to malicious sites can be sent via email, and recipients are lured with tasty promotions and discounts. This year, the Turkish Ministry of Trade has already warned Russian tourists about fake hotel deals.
Similar schemes are used to «sell» rail and air tickets, whereby victims risk not only losing money, but handing their personal data to the scammers.
Dangerous dating
With the mass shift to online, people have started making more use of dating apps. So too have scammers, who create fake profiles with the goal of extracting money or personal information from gullible users. For example, an attacker might ask the victim to pay for a trip to the cinema together, or drop a link to their profile on another social network. Of course, these are tricks. The money for movie tickets or account credentials will go straight to the scammers.
Subscriptions to services
In today’s world, many people have multiple subscriptions to music- and movie-streaming apps and cloud services.
Fraudsters exploit this by sending emails prompting victims to take out or renew subscriptions to various platforms. We wrote about one such scenario in our recent analytical report: the victim received an email about the expiry of a trial period, warning that a subscription fee would now be charged. A phone number was supplied on which to «cancel» the subscription if desired. On top of phishing, this campaign employs an uncommon technique: Fake call centers. After calling the number, the user, following the operator’s instructions, downloaded a malicious file.
Investments in cryptocurrency and oil & gas
The topic of investing is becoming increasingly popular with ordinary users, most of whom are not familiar with the rules of information security, so scammers are rushing to capitalize on this trend.
Cybercriminals create fake websites that imitate the resources of well-known companies, then offer users the chance to make money by investing in, say, cryptocurrency or oil & gas. To obtain funds, cybercriminals sometimes even set up entire investment platforms with a minimum deposit to start trading. There have also been cases of fraudsters, under the guise of a well-known bank, offering victims financial rewards from investors as a thank you for being active banking users. To receive the payment, as usual, they were asked to fill out a short application form and provide bank card details to verify the account.
Forecasts
Most of the above-listed topics never go out of fashion, but are simply updated and modified by attackers year after year.
In 2022, we again expect to see a large number of phishing campaigns in connection with various major events, including the FIFA World Cup and the Winter Olympics.
In light of current trends, there is a high probability of attacks related to new films and TV shows, for example, 2022 will see the release of a new series based on the works of J. R. R. Tolkien. Tolkien’s massive fan base makes this one of the most eagerly anticipated releases of the year, by viewers and cybercriminals alike.
We may also see attackers taking advantage of the launch of the digital ruble prototype to create phishing sites and sell fake cryptocurrency. And, continuing the financial theme, it is worth mentioning the ongoing development of social engineering-based fraud in the field of investments. The victims in this case are private investors persistently targeted by scammers under the guise of professional investors, authors of training courses, and fake investment platforms.
Overall, we expect the phishing-as-a-service model to expand and proliferate. This model is based on collaboration between cybercriminals and the buying and selling of off-the-shelf solutions, such as fake websites or malicious scripts.
To avoid the damaging consequences of phishing, you just need to know what to look for and follow some simple information security rules:
- Always check the sender’s address.
- Never click suspicious links.
- Never enter credentials or payment data without making sure the website is real.
- Book hotels and tickets only on trusted resources; the same applies to subscriptions.
To prevent malware infection, scan all files received. In a corporate environment, use sandboxes for this.
