Key figures and trends
In Q4 2022, the number of incidents decreased by 5% compared to the previous quarter, although it still remained quite high—15% more than in the same period in 2021. The share of mass attacks continued to grow, increasing by 2%. Successful cyberattacks most often resulted in leakage of confidential information (51%) and disruption of core activity (36%). We've seen outages in critical infrastructure, and major leaks of user data and product source code.
Spyware is on the rise
The share of attacks which use spyware is growing: 17% of such attacks were carried out against organizations, 49% against individuals; this is respectively 5 p.p. and 3 p.p. more than in the last quarter. Attackers are creating new malware and working to expand its functionality: for example, the new Aurora stealer can exfiltrate data not only from browsers or the clipboard, but also directly from the device's disk. The distribution of spyware under the "malware as a service" model means that even inexperienced attackers can use it: for example, the new BlueFox stealer analyzed by Positive Technologies researchers is actively promoted on the underground market in this way. In addition, we've seen an increase in cases of embedding spyware code into Python packages. This can lead to growing numbers of supply chain A cyberattack in which attackers infiltrate a company by compromising software or hardware providers. For example, criminals can inject malicious code into a product's source code or distribute malicious updates to infect the target organization's infrastructure. attacks leading to compromise of IT companies' networks.
Botnets and RATs
In Q4, we saw increased usage of remote-control malware: the share of attacks on organizations using such malware increased by 6 p.p. compared to the previous quarter. New botnets were discovered: MCCrash, which can attack Windows and Linux systems, and GoTrim, which hacks into vulnerable WordPress sites and can evade bot protection. Old threats have also returned: Cyble researchers spotted the SmokeLoader botnet spreading the new Laplas cryptoclipper A type of malware that checks the clipboard for the presence of a cryptowallet address and replaces it with the attacker's address. the botnets Emotet—which has returned after a lull—and QakBot were used to deliver various malware, including Black Basta ransomware and Brute Ratel and Cobalt Strike beacons A malicious payload used to gain remote access to compromised systems, collect data, or load additional malware. .
New cross-platform ransomware and encryption methods
The RansomExx and Qilin groups have acquired cross-platform versions of their ransomware written in Rust, allowing them to target Windows and Linux systems. Attackers are increasingly using intermittent file encryption with a certain byte step; this approach makes encryption fast and less noticeable to monitoring tools due to fewer operations on the encrypted file and its similarity to the original. After a lull period, wipers disguised as ransomware became active again. Such malware converts data and leaves a ransom note, but payment will not help to return the data, which actually cannot be recovered.
The list of high-profile attacks continues to grow: a ransomware attack on the government of the French overseas department of Guadeloupe disabled almost the entire state IT infrastructure; The Daixin Team ransomware group managed to steal information about five million AirAsia passengers and encrypt its servers.
A growing number of cyberattacks on the insurance sector
In Q4, we noticed an increase in the number of successful cyberattacks on insurance companies—more than double the previous quarter. In 73% of attacks, information about clients was leaked: mostly personal data, and in some cases medical information. The stolen data is sold on the shadow market or used by attackers for subsequent attacks. Ransomwarers are eager to get their hands on insurance information, because if they find out that an organization has cyberinsurance that covers the ransom, it's an easy target: such organizations are very likely to pay up.
Attacks on IT companies and their cross-industry consequences
IT companies present prime targets for attackers, since compromising them can lead to further attacks on their clients—users of the products and services (for example, supply chain and trusted relationship attacks In a trusted relationship attack, criminals hack the infrastructure of a third-party company whose employees have legitimate access to the main target's resources. )—with serious consequences. The number of incidents related to IT companies increased by 18% in Q4. 62% of them used malware; these were predominantly ransomware attacks aimed at stealing confidential information and obtaining a ransom.
The victims included software vendors for organizations from various industries. The attack on Supeo, an IT services provider for a Danish train operator, became a sensation: because of the hackers' actions, trains all over the country were stopped for several hours. The provider's application failed to function correctly, preventing train engineers from accessing critical information such as railroad maintenance notices and speed limits. As a result, the train operations had to be suspended.
Individuals are increasingly being attacked on social networks and in instant messengers
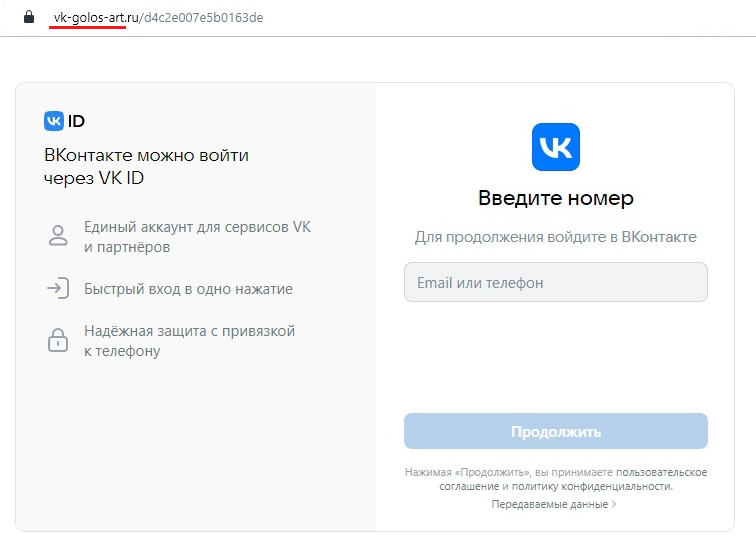
In Q4, the share of attacks on individuals out of the total number of attacks increased by 5 p.p. compared to the previous quarter. This number continues to grow as successful attacks on individuals through social networks and instant messengers become more frequent. In Q3 2022, 18% of social engineering attacks targeted social media users, while instant messaging and SMS were used in 15% of such attacks. In Q4, the attackers were no less active: 19% of attacks were directed at users of social networks, and in 17% of social-engineering attacks messengers and SMS messages were used. The amount of stolen credentials is also increasing: from 39% in Q3 to 44% in Q4.
Most of the successful attacks using social networks and messengers are aimed at collecting credentials and hacking accounts; compromised accounts are then used for further attacks on users. In one of these attacks, the scammers asked users to vote online—supposedly for a relative or acquaintance in a children's contest—while the link took them to a phishing site. In another attack, recorded in December, many Telegram users received fake messages about a gift Telegram Premium subscription. To activate the subscription, users were asked to enter an authorization code—but this just led to the account being compromised and the further distribution of phishing emails to the victim's contacts.
Account details are not the only thing criminals want to get hold of; personal data and payment data are also in demand. In one attack targeting Indian citizens, the attackers used an unusual tactic: they tracked the messages of Twitter users complaining about the Indian Railway Catering and Tourism Corporation and contacted them, pretending to be customer support representatives and requesting personal information.
To protect against cyberattacks, we first and foremost recommend following our general guidelines on personal and corporate cybersecurity. Considering the types of incidents we've seen in Q4 2022, we strongly recommend that you treat incoming emails and messages from instant messengers and social networks with caution: check the sender and don't click on any suspicious links to avoid becoming a victim of social engineering or having your device compromised by malware. Download applications only from trusted sources, use open source code only after checking it for malicious modules, use file backup solutions, and install security updates in a timely manner. In addition, we advise to thoroughly investigate all major incidents to identify points of compromise and vulnerabilities exploited by attackers, and to swiftly make sure that the criminals did not leave any backdoors. You can strengthen security at the corporate perimeter with the aid of cutting-edge security tools, such as web application firewalls (WAF) for protecting web resources. To prevent malware infection, we recommend using sandboxes to analyze the behavior of files in a virtual environment and detect malicious activity.
Attack consequences
Attacks in Q4 led to a range of different consequences, varying in both character and impact: successful cyberattacks affected both small business and groups of companies, and sometimes even entire states. The criminals' main aim was to obtain confidential information. In addition, we've seen criminal actions leading to large financial losses and also disruptions to the core activities of organizations and sometimes critical infrastructure.
The top 5 attacks in Q4 that had a negative impact and wider repercussions
- An attack on the electricity provider ECG in Ghana. As a result of the ransomware attack, customers were unable to pay for their electricity, leading to power outages. In some areas of the country, residents had their power cut off for several days.
- The insurance company Medibank was the victim of a ransomware attack that disrupted the operation of the company's online services and IT infrastructure, after which the attackers made information about its clients publicly available, including health status and diagnoses.
- Passwords and other credentials are highly sought by criminals. Hacking into the LastPass password vault allowed attackers to obtain very valuable data such as the URLs, IP addresses, logins, and encrypted passwords of the customers.
- Attacks on developers of multi-factor authentication and identification solutions are becoming more frequent: in Q4, hackers carried out yet another successful cyberattack on Okta, the fourth time in 2022. The criminals managed to copy the source code of the Workforce Identity Cloud product, which is used to identify users and manage privileged access in the cloud.
- One of the largest mining pools, BIT Mining, was attacked by cybercriminals. As a result, users of BTC.com had their assets stolen, valued at approximately 700 thousand dollars, and the pool itself lost 2.3 million dollars in cryptocurrency. Later, it was discovered that the attackers managed to send the stolen assets to the Tornado Cash mixer, and the value of BIT Mining shares dropped by 20%.
Q4 was marked by high-profile leaks of data stolen through cyberattacks on organizations. In such attacks, the criminals were most often aiming to steal personal data (38%) and intellectual property (20%).
The most notable leaks in Q4
- The leak of the UEFI (BIOS) source code of Intel's Alder Lake processors: 5.97 GB of information—proprietary source code, private encryption keys, logs, and compilation tools—were released publicly on GitHub. This type of data can be used to search for vulnerabilities, including ones that allow attackers to introduce a bootkit.
- A phishing attack on Dropbox resulted in the theft of 130 repositories containing information about current and former customers, as well as the API keys of Dropbox developers.
- The Ragnar Locker ransomware gang released information stolen from an attack on the Zwijndrecht Municipal Police Department (Belgium). Data on fines, reports on crimes and investigations, and information about department employees was leaked.
- The NLB group made public a database from the travel company Level.Travel, with information about 400,000 travel bookings and the personal data of 900,000 people. The database contained full names, contact information, IP addresses, and passport details.
Statistics
65% of attacks were targeted
19% of attacks were aimed at individuals
About the report
This report contains information on current global information security threats based on Positive Technologies' own expertise, investigations, and reputable sources.
We estimate that most cyberattacks are not made public due to reputational risks. As a consequence, even companies specializing in incident investigation and analysis of hacker activity are unable to quantify the precise number of threats. Our research seeks to draw the attention of companies and ordinary individuals who care about the state of information security to the key motives and methods of cyberattacks, as well as to highlight the main trends in the changing cyberthreat landscape.
This report considers each mass attack (for example, а phishing email sent to multiple addresses) as one incident, not several. For explanations of terms used in this report, please refer to the Positive Technologies glossary.
